Cybersecurity Companies Los Angeles
Cybersecurity companies in Los Angeles provide essential protection against evolving threats like ransomware and phishing by offering proactive, 24/7 monitoring, encryption, and compliance support. Costs vary based on business size and complexity, but managed services offer scalable, predictable pricing that’s far lower than the cost of a breach. Choosing a local, experienced provider ensures faster response times, tailored solutions, and stronger long-term security for your business.

Cybersecurity Companies Los Angeles: Top Firms & Costs
The digital landscape in Southern California is a shark-infested territory where your data is the primary bait. For businesses operating in the sprawl, finding elite cybersecurity companies in Los Angeles isn't just a line item—it’s the difference between business as usual and a catastrophic ransomware shutdown. In Los Angeles, the demand for "boots on the ground" security solutions is skyrocketing as localized threats evolve. Selecting a provider who understands the specific digital infrastructure of our region is a high-stakes decision that dictates your long-term survival.
Key Takeaways
- Data Fortification: Specialized services act as a digital bulkhead against sophisticated breaches and systemic failures.
- Cost Variables: Pricing isn't one-size-fits-all; it scales based on your seat count, risk surface, and the complexity of your stack.
- Managed Vigilance: 24/7 monitoring ensures that while you sleep, an active defense is hunting for anomalies.
- The Local Edge: Los Angeles firms offer the low-latency response and face-to-face accountability that remote giants lack.
- Risk Mitigation: Proactive investment in security drastically lowers the "blast radius" of potential cyber incidents.
Why Are Cybersecurity Companies in Los Angeles Essential for Modern Business?
Cybersecurity companies in Los Angeles provide the heavy-duty shielding required to block network intrusions, data exfiltration, and operational sabotage. By deploying advanced threat detection and rigorous encryption protocols, these firms act as a private security detail for your digital assets. In a city where a single breach can trigger massive litigation and reputational collapse, having local experts who can pivot as fast as the hackers do is the only way to maintain a defenseless posture.
What Types of Security Services Protect Your Bottom Line?
The Strategic Framework for Defense
- Perimeter Hardening: Deploying industrial-grade firewalls and intrusion prevention systems (IPS) to kill threats at the gate.
- Scrub inbound traffic for malicious signatures.
- Segment internal networks to prevent lateral movement by attackers.
- Data Sanitization and Vaulting: Implementing AES-256 encryption for all data at rest and in transit.
- Ensure sensitive client records are unreadable to unauthorized eyes.
- Establish immutable backups that ransomware can't touch.
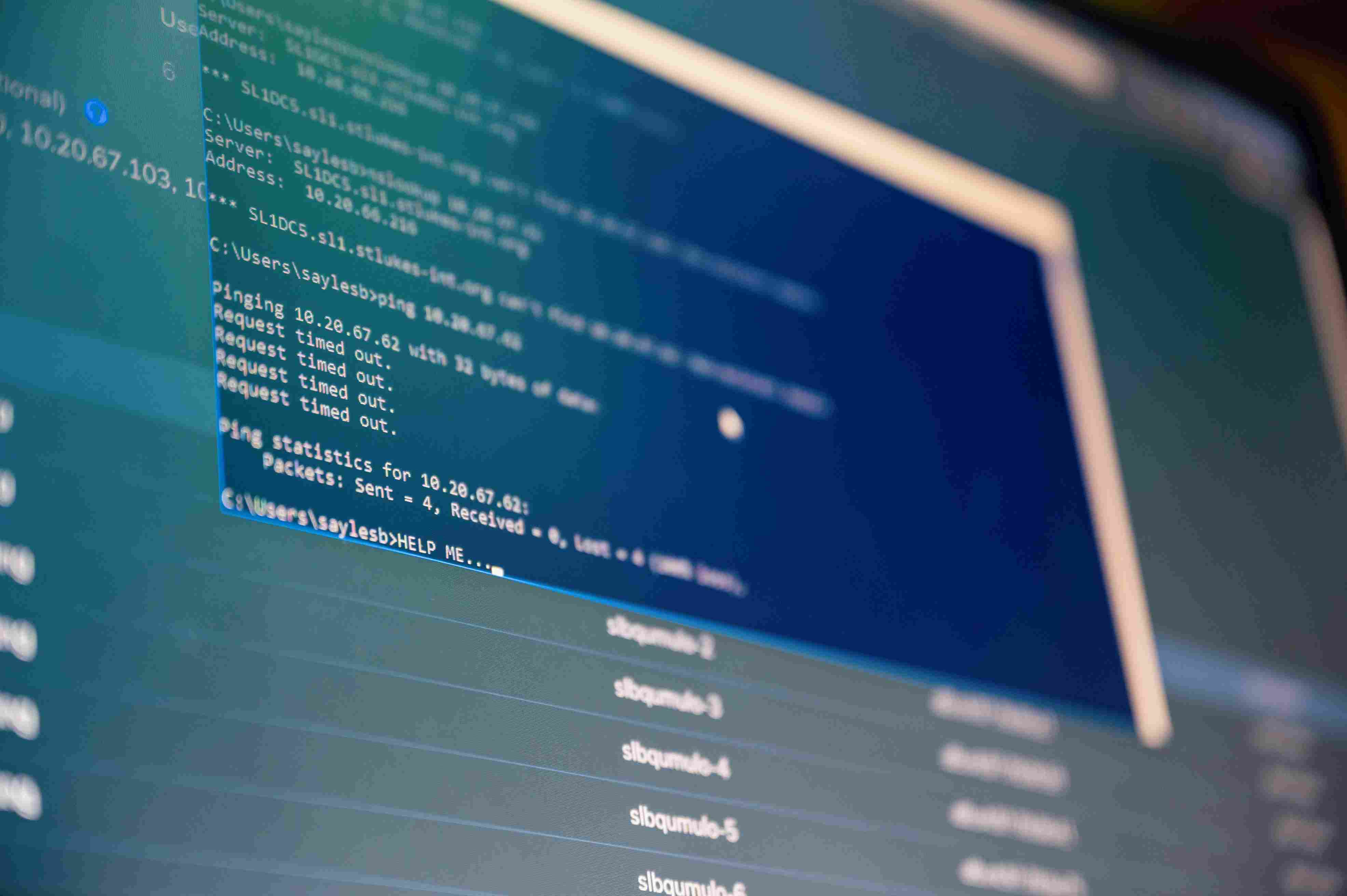
- Active Threat Hunting: Utilizing 24/7 Security Operations Centers (SOC) to monitor for "low and slow" attacks.
- Identify anomalous login patterns from foreign IPs.
- Execute rapid incident response to isolate infected workstations before they spread.
- Governance and Compliance: Aligning your IT stack with regulatory frameworks like HIPAA, PCI-DSS, or CMMC.
- Conduct quarterly audits to identify "drift" in security settings.
- Provide the documentation needed to pass high-stakes insurance renewals.
How Do You Compare Traditional IT to Modern Cybersecurity?

Which Core Entities Define the Security Landscape?
- Endpoint Detection and Response (EDR): The "on-device" security that watches for suspicious file behavior rather than just known viruses.
- Zero-Trust Architecture: A security model that assumes every user and device is a potential threat until verified.
- Phishing Simulation: Training your "human firewall" by sending fake bait emails to see who clicks.
- SOC (Security Operations Center): The physical or virtual command center where analysts watch your network in real-time.
What Makes a Cybersecurity Provider Truly Elite?
When you are vetting cybersecurity companies in Los Angeles, look for "scar tissue"—real experience across diverse industries like healthcare, finance, and manufacturing. You need a firm that uses hardened toolsets, not just off-the-shelf software, and guarantees response times measured in minutes, not days. Transparent communication is the bedrock here; if they can't explain the threat in plain English, they probably don't understand the solution. True pros offer "elastic" security that expands as your headcount grows without leaving gaps in the fence.
Expert Perspective: The "Shadow IT" Trap
Pro Tip: The biggest threat to your Los Angeles business isn't a hacker in a hoodie; it's your own employees using "Shadow IT"—unauthorized apps like personal Dropbox or Slack accounts to move company data. Even the most expensive firewall is useless if your staff is bypassing it for convenience. Always pair your technical tools with a strict "Acceptable Use Policy" and forced Multi-Factor Authentication (MFA) across every single login. If it's not behind MFA, it's not secure.
How Does Sentant Overhaul Your Digital Safety?
At Sentant, we don’t just "monitor" your systems; we fortify them using the same aggressive tactics that attackers use. Our mission is to strip away the complexity of security while hardening your environment against the specific strains of malware targeting the West Coast. From deep-packet inspection to cloud-native security, we provide the air cover your business needs to scale. We recognize that no two companies have the same DNA, so we build bespoke defense layers that actually fit your workflow instead of slowing it down.
What Should You Expect to Pay for Cybersecurity in Los Angeles?
Pricing for cybersecurity companies in Los Angeles is a sliding scale dictated by the "value of the prize" you are protecting. Small shops might see entry-level managed security starting at a few hundred dollars a month, while mid-sized enterprises requiring full-spectrum SOC services and compliance management can expect to invest thousands. Managed services are generally the move here because they offer a predictable monthly burn. Remember, the "cost" of security is a drop in the bucket compared to the average $4 million price tag of a localized data breach.
Why Is a Local la Firm Better Than a National Giant?
Partnering with cybersecurity companies in Los Angeles gives you a tactical advantage when things go sideways. If a server room experiences a hardware failure or a local disaster, having a technician who can be on-site in Santa Monica or Downtown LA in an hour is invaluable. Local firms understand the regional regulatory climate and the specific "industry clusters" that define our economy. You aren't just a ticket number in a queue; you're a neighbor whose uptime directly impacts the local community.
How Do You Vet the Right Security Partner?
Finding the right fit requires looking past the marketing gloss. Start by scrutinizing their actual track record—ask for case studies where they successfully neutralized a live threat. Check for high-level certifications like CISSP or CISM, which prove they aren't just "tech hobbyists." Availability is the next big hurdle; if they don't offer 24/7 support, keep walking. Finally, weigh their service packages against your specific risk profile to ensure you aren't paying for "bloatware" or, worse, leaving your most vulnerable assets exposed.
What Are the Most Common Threats Facing LA Businesses?
The reality on the ground is that phishing is still the #1 entry point for "the bad guys." Whether it's a fake invoice or a spoofed CEO email, your team is being targeted daily. Beyond that, ransomware continues to evolve, now using "double extortion" where they steal your data and lock your systems. Without a "Master Craftsman" approach to security, these risks can paralyze your operations. Continuous training and robust technical barriers are the only way to stay ahead of the curve.
Putting Your Cybersecurity Strategy into Motion
Navigating the treacherous waters of digital defense requires more than just a standard antivirus; it requires a partnership with a firm that understands the high-velocity nature of the Los Angeles business world. By prioritizing a "security-first" culture and leveraging local expertise, you transform your IT from a vulnerability into a competitive fortress.
Don't wait for a "System Encrypted" screen to realize your defenses were lacking. Call (888) 555-0199 today to schedule a comprehensive security audit and secure your firm's future among the top cybersecurity companies in Los Angeles.
Frequently Asked Questions
How much do cybersecurity services cost in Los Angeles?
Pricing is highly variable, typically ranging from $100 to $500 per user per month, depending on the depth of the stack. Managed Service Providers (MSPs) provide the best value by bundling licensing, monitoring, and support into a single, predictable monthly fee that scales with your growth.
What services do cybersecurity companies provide?
Standard offerings include managed firewalls, Endpoint Detection and Response (EDR), Multi-Factor Authentication (MFA) implementation, and 24/7 SOC monitoring. Higher-tier firms also handle regulatory compliance (like HIPAA or SOC2) and conduct "penetration testing" to find weaknesses before hackers do.
Why are cybersecurity services important?
They serve as the primary insurance policy against data theft, financial fraud, and catastrophic system downtime. In the current landscape, a single unpatched vulnerability can lead to a total loss of client trust and massive regulatory fines that most businesses never recover from.
Can small businesses afford cybersecurity services?
Absolutely. Modern security is modular, allowing small businesses to start with "the essentials"—like email filtering and managed backups—and add layers as their budget allows. Many local providers offer "lite" versions of enterprise tools specifically designed for the SMB market.
How do I choose the best cybersecurity company?
Prioritize firms with local Los Angeles references, specific expertise in your vertical, and a proactive communication style. Look for transparency in their pricing and a clear roadmap for how they plan to mature your security posture over the next 12 to 24 months.
Will Pizzano, CISM is Founder of Sentant, a managed security and IT services provider that has helped dozens of companies achieve SOC 2 compliance. If you’re interested in help obtaining SOC 2 compliance, contact us.

.jpeg)