Why Startups Need CyberSecurity
Cybersecurity is a strategic necessity for startups because early-stage companies often hold valuable intellectual property and customer data while operating with limited defenses. A single breach can trigger financial losses, operational shutdowns, and irreversible reputational damage that many startups cannot survive. By adopting basic security practices early—such as multi-factor authentication, least-privilege access, employee training, and incident response planning—startups turn security into a competitive advantage that protects growth, builds trust, and strengthens investor confidence.

Why Startups Need CyberSecurity: The Strategic Imperative
The contemporary venture space is characterized by a relentless pursuit of disruption, and a deep structural frailty underpins this digital gold rush. For a fledgling company, dismissing defensive design as secondary consideration is not just tactical short-sightedness; it's an invitation for advanced adversaries to deconstruct a vision before it ever scales. Building a strong position of “why startups need cyberSecurity” ensures that intellectual property is an asset rather than a liability.
Key Takeaways
- Target maximum-value assets in under-resourced organizations, which may not always be aware of exposure to significant volumes of data.
- Calculate the domino effect of a breach from near-term cash crunches to reputation-ending insolvency.
- Enforce hygiene practices such as MFA and least privileged access to prevent basic attack infrastructures.
- Drive the most security value from investments by using higher-ROI cloud patterns and well-thought-out incident response approaches.
- Counter the odds through early-stage resilience as a competitive advantage to raise institutional capital and strengthen customer acquisition.
Vulnerabilities in the Emerging Enterprise Architecture
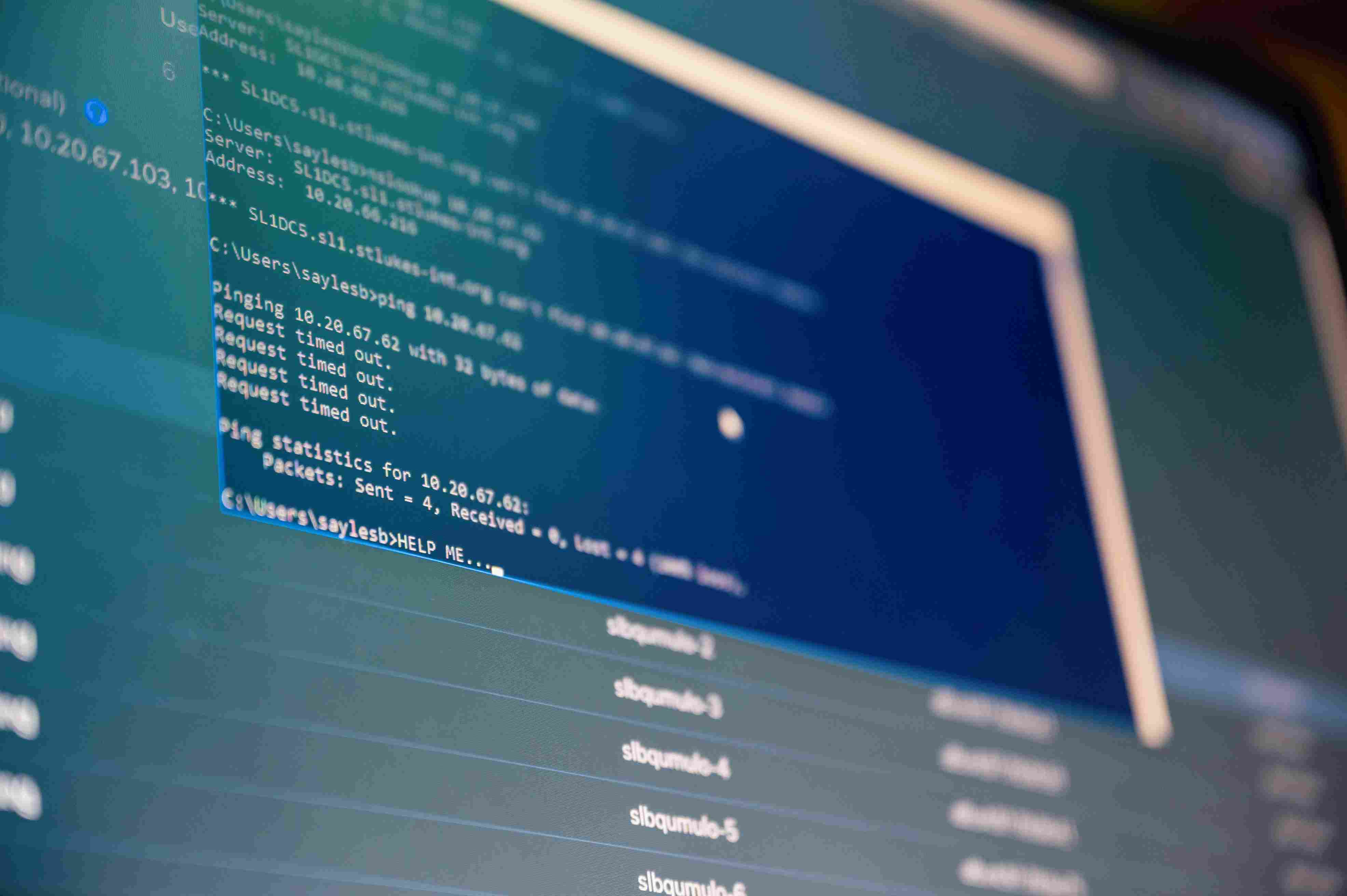
Lean Operations, Expanded Attack Surfaces
In the sprint toward a Minimum Viable Product, dedicated security engineering is frequently sidelined. This reliance on generalist vigilance creates significant blind spots in the [City] tech corridor, where a single phishing oversight can bypass an entire year of development.
The Valuation of Proprietary Assets
Startups often house concentrated repositories of unpatented trade secrets, sensitive consumer data, and disruptive codebases. To a digital mercenary, these less-fortified environments represent a high-yield opportunity with significantly lower friction than an enterprise-grade fortress.
Growth at the Expense of Integrity
When aggressive market penetration dictates the budget, digital defense is often pushed to the periphery. This creates a "perfect storm" for exploitation, as rapid scaling without a secure underlying framework results in a fragile infrastructure that cannot withstand a directed breach.
The True Cost of Digital Negligence
Financial Insolvency
A security compromise triggers an immediate drain on capital reserves. Beyond the initial remediation costs, firms face regulatory fines, class-action litigation, and the potential for extortionate ransom demands. For a bootstrapped venture, these liabilities often exceed total lifetime funding.
Operational Stagnation
Threat actors focus on paralyzing mission-critical systems. When a platform goes dark, product deployments stall and customer churn accelerates. This loss of momentum in the high-stakes [City] market is often the precursor to a permanent shutdown.
Reputational Erasure
Trust is the most difficult asset to recover once liquidated. In a transparent digital economy, news of a breach compromises the brand’s integrity instantly. When investors perceive a lack of custodial responsibility, follow-on funding rounds evaporate, turning a once-promising unicorn into a cautionary case study.
Architecting a Resilient Defensive Perimeter
Building a defensible posture does not require the capital outlay of a Fortune 500 firm. It requires a disciplined, "Master Craftsman" approach to system integrity:
- Instill a culture of security awareness by training personnel to recognize sophisticated social engineering and enforcing rigorous credential management.
- Enforce the Principle of Least Privilege (PoLP) to ensure that internal access is restricted to essential functions, effectively siloing potential points of failure.
- Vet third-party cloud integrations with extreme prejudice, prioritizing providers with audited encryption standards for data both in transit and at rest.
- Formalize a comprehensive Incident Response Plan (IRP) that outlines clear recovery paths. Executing regular "fire drills" ensures the leadership team can maintain composure when the digital sirens sound.
Security as a Catalyst for Scalable Growth
Prioritizing a hardened infrastructure is a sophisticated business move that pays dividends across the lifecycle of the firm. By addressing Why Startups need CyberSecurity, leadership can:
- Cement Customer Reliability: Demonstrating professional data stewardship fosters long-term retention and higher Lifetime Value (LTV).
- Accelerate Institutional Funding: Sophisticated VC firms perform deep technical due diligence; a secure infrastructure signals a de-risked investment.
- Navigate Global Markets: Operating with a proactive defense allows a founder to focus on innovation without the looming threat of catastrophic data exfiltration.
Sentant: Engineered Security for High-Growth Firms
Sentant prioritizes the human element of the defensive stack by providing tailored employee-training modules designed to neutralize phishing and social engineering risks. Our engineers work alongside leadership to develop incident response strategies that ensure a coordinated, rapid recovery following any disruption. As a strategic partner, Sentant provides continuous environmental monitoring and rigorous regulatory compliance, utilizing proactive penetration testing to identify weaknesses before they are exploited in the wild.
Frequently Asked Questions
1. Why are emerging ventures targeted specifically by threat actors?
Small-cap firms often possess high-value intellectual property but lack the hardened perimeter of established corporations. Attackers view these organizations as "soft targets" where the effort-to-reward ratio is highly favorable.
2. Is a single compromise truly capable of dissolving a company?
Absolutely. Beyond the immediate technical recovery, the legal liabilities and the permanent loss of institutional trust can create a deficit that most early-stage balance sheets cannot absorb.
3. Does effective defense require a massive capital expenditure?
No. High-impact security is about discipline, not just software. Implementing MFA, strict access controls, and rigorous team training provides an exponential return on investment without requiring a seven-figure budget.
4. Can we defer security implementation until after our Series A?
Deferment is a high-stakes gamble. Retrofitting security into a bloated, legacy infrastructure is far more expensive than building a secure foundation from Day 1. Early adoption protects your valuation and prevents costly architectural reworks.
5. How does a secure posture contribute to my bottom line?
It functions as a force multiplier for growth. A secure enterprise experiences fewer disruptions, passes due diligence faster, and builds a brand synonymous with reliability. Investing in Why Startups need CyberSecurity is the most effective way to protect your path to an exit.
Will Pizzano, CISM is Founder of Sentant, a managed security and IT services provider that has helped dozens of companies achieve SOC 2 compliance. If you’re interested in help obtaining SOC 2 compliance, contact us.

.jpeg)