How Long Does It Take to Get SOC 2 Compliance?
Achieving SOC 2 compliance can take anywhere from 2 to 12+ months depending on your organization's security maturity and the type of report — Type 1 (faster) or Type 2 (more comprehensive). Type 1 typically takes 2–4 months, while Type 2, which requires a longer observation window, can take 6–12 months or more. With the right preparation, documentation, and expert support like Sentant’s, businesses can streamline the process and build trust with customers more efficiently.

SOC 2 compliance is something that every business dealing with customer data dreams of achieving. And even more so for SaaS providers or cloud-based technology companies. It assures customers, partners, and investors that serious measures are addressed in security and that systems exist to protect sensitive information.
But how long would it take to get the report for your SOC 2?
This is the answer; it depends.
You could spend anywhere from many months to more than a year just working on your SOC 2 preparation. It will depend on how mature the security program is and how well-prepared you are. The length also varies for the type of SOC 2 report you want, and whether you use tools like compliance automation to speed up the overall project.
We will look at the typical SOC 2 journey from pre-audit preparation to the final report. Then, we’ll give you realistic timeframes based on the type of audit you ultimately decide to choose.
SOC 2 Type 1 vs. Type 2: What’s the Difference?
Before we dive into timelines, it’s important to understand the difference between SOC 2 Type 1 and SOC 2 Type 2.
- SOC 2 Type 1 looks at your security controls at a specific point in time. It answers the question: "Have you designed and implemented the right controls?"
- SOC 2 Type 2 goes a step further. It reviews those same controls over some time (typically 3–12 months) to verify that they are working effectively in practice.
SOC 2 Type 1 is generally faster to complete and a great starting point for early-stage companies. SOC 2 Type 2 takes longer but offers stronger proof of your ongoing security practices — a big plus for enterprise customers.
SOC 2 Type 1 Timeline: 2 to 4 Months
For many businesses, especially startups, SOC 2 Type 1 is the first step toward building trust with customers and investors. Here’s what to expect:
1. Pre-Audit Preparation (1–3 months)
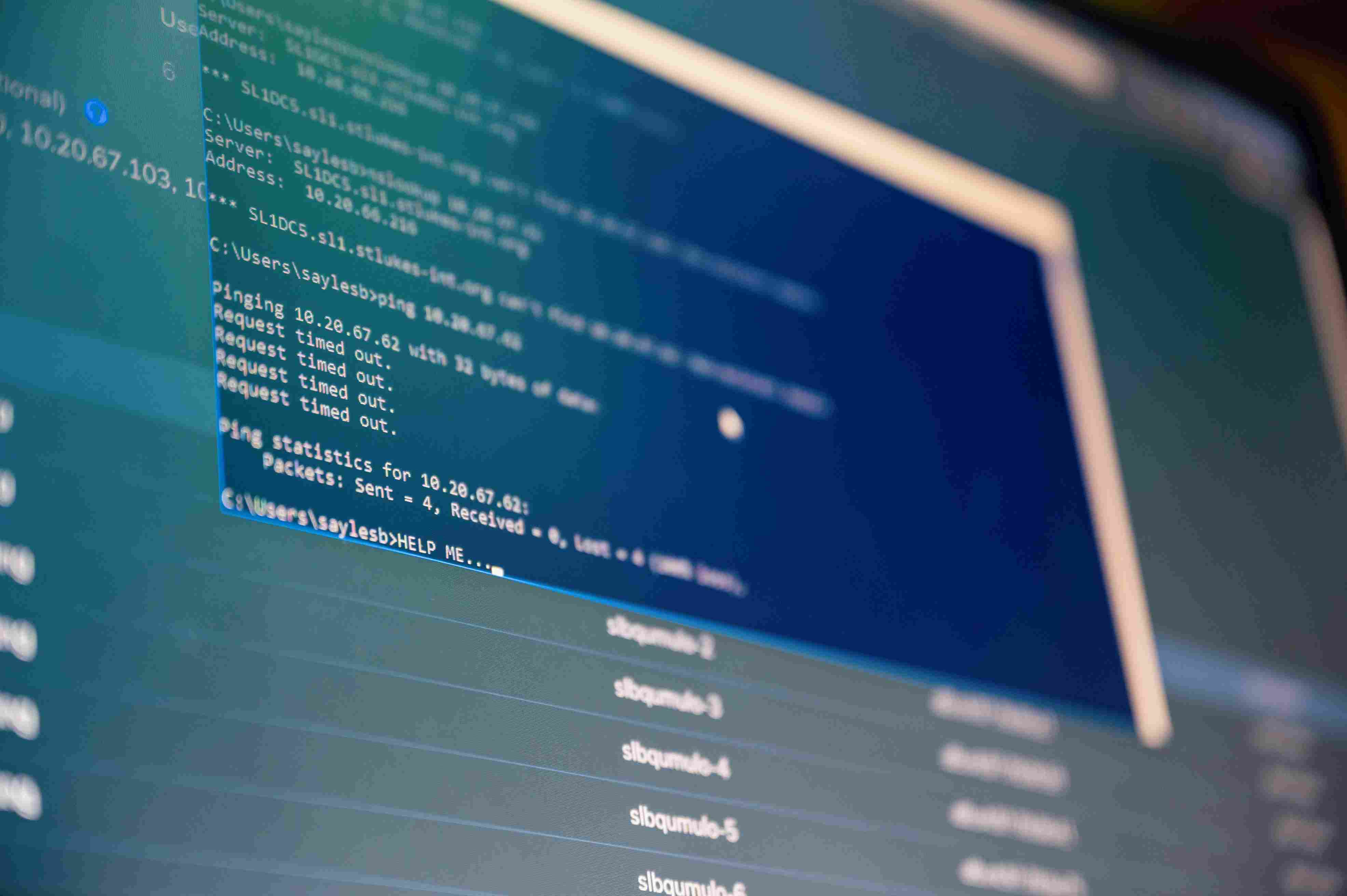
Before you start the audit, you’ll need to review and update your internal controls. This includes:
- Implementing access controls and identity management
- Encrypting data at rest and in transit
- Creating security policies
- Conducting risk assessments
- Documenting processes
- Collecting evidence of compliance
If you already have many of these controls in place, this phase might only take a few weeks. If you’re starting from scratch, expect to spend a few months getting ready. Sentant can help here — from identifying gaps to helping you implement the right technical and policy controls.
2. The Audit (2–5 weeks)
An AICPA-level auditor will review your controls and evidence through interviews, document reviews, and system walkthroughs. The more prepared you are and the faster you respond to requests, the smoother the overall process will be.
3. Report Delivery (2–6 weeks)
the auditor compiles your SOC 2 Type 1 report. This report's purpose is to confirm that your controls are properly designed and implemented. You could then share this report with customers and prospects to demonstrate that you take data security seriously.
SOC 2 Type 2 Timeline: 6 to 12+ Months
SOC 2 Type 2 is a type of extensive assessment or audit, which proves how well the security controls work as time passes. It is the preferred standard for companies that deal with regulated industries or enterprise clients.
1. Pre-Audit Preparation (1-3 months)
This phase resembles Type 1. You will need to scan your systems, close potential gaps, install required controls, and collect evidence. If you have already been through SOC 2 Type 1, this part might take less time. Otherwise, be prepared to allocate a few months to prepare for the auditing purposes.
2. Observation Window of 3-12 months
This is the main difference between Type 1 and Type 2. You choose a period - usually 3, 6, 9, or 12 months - when the operation of your controls will be observed. Your auditor won't be watching you every day during this period, but he or she will later verify that your controls were consistently followed.
- Shorter observation windows (3–6 months) can get you certified faster, but may not satisfy some enterprise clients.
- Longer windows (9–12 months) show ongoing reliability but require more time and effort.
Most companies start with a shorter window for their first audit, then expand to 12 months in future audits.
3. Audit & Review (1–3 weeks)
Once the observation period ends, the auditor will review your logs, records, and documentation from that entire time frame. This can be a bit more involved than Type 1, since they’re evaluating how consistently you followed your processes.
4. Report Delivery (2–6 weeks)
After the audit, the auditor delivers your official SOC 2 Type 2 report. This document provides detailed proof of your security controls and how well they operated over time. It’s a valuable trust signal for enterprise deals and customer relationships.
How to Speed Up Your SOC 2 Process
SOC 2 doesn’t have to be overwhelming. Many companies waste time with manual processes, scattered documentation, and reactive decision-making. Sentant works with businesses to cut through the noise.
Here’s how we help speed up your SOC 2 timeline:
- Assess your current security posture and identify gaps
- Build or refine policies tailored to SOC 2 Trust Services Criteria
- Implement core technical controls like IAM, encryption, and vendor risk management
- Use audit-ready frameworks to centralize documentation and evidence
- Recommend automation tools to collect logs and maintain audit trails
Whether you're starting from scratch or scaling up your compliance efforts, our hands-on guidance ensures you stay on track.
Final Thoughts
So, how long does it take to get SOC 2 compliant? The answer depends on your starting point and goals:
- SOC 2 Type 1: ~2 to 4 months
- SOC 2 Type 2: ~6 to 12 months
Both reports require strong preparation and good documentation practices. The more organized you are, the faster it will go — and the fewer surprises you’ll face.
At Sentant, we help growing tech companies move faster and smarter through the SOC 2 process. With the right support, you don’t have to choose between compliance and momentum. You can have both.
Will Pizzano, CISM is Founder of Sentant, a managed security and IT services provider that has helped dozens of companies achieve SOC 2 compliance. If you’re interested in help obtaining SOC 2 compliance, contact us.