What are SOC 2 Compliance Requirements
SOC 2 compliance is a security framework that verifies a company’s ability to protect customer data through five Trust Services Criteria: security, availability, confidentiality, processing integrity, and privacy. It requires independent audits to assess an organization’s controls, with Type 1 evaluating them at a single point and Type 2 measuring their effectiveness over time. Sentant simplifies this process through automation—streamlining evidence collection, integrations, and audits to help businesses achieve compliance faster and strengthen trust with customers.

What are SOC 2 Compliance Requirements by Sentant
Businesses all over the world use compliance for SOC 2 to show their security posture and gain customer trust. SOC 2 compliance is now a standard for most organizations that handle customer data.
For organizations that are going through the process for the first time, it can be time-consuming and complex. This guide provides an overview of SOC 2 and the criteria that you will need to prepare your audit. It also offers tips on how to get started.
Key Takeaways
- SOC2 compliance requirements: Defined and implemented by the Trust Services Criteria.
- Trust Services Criteria: The SOC 2 audits are conducted based on the five criteria of risk-driven audits - security, availability, confidentiality and processing integrity.
- Controls that are tailored to your company: Since SOC 2 is a flexible and risk-based model, each organization defines its own controls in order to meet the criteria.
- Audit Process: An independent auditor examines your controls, issues a SOC 2 Report, which is shared with customers, prospects, and business partners.
- Required criteria vs. Optional Criteria: Security must be met; the four other TSC categories are only applicable if they are relevant to your operation
- SOC2 Type 1 vs. Type 2 Reporting: Type 1, audits controls in a single moment; Type 2, tests effectiveness over time
- Compliance timeline: Meeting SOC 2 requirements and auditing them typically takes around a year.
- Automation Benefits: Tools such as Sentant, with their integrations, evidence gathering, and built-in audit access, reduce SOC2 timelines.
What is a SOC 2 Compliance Report?
You'll need a third-party auditor to evaluate your information security practices to determine if they meet SOC 2 compliance requirements. The auditor will create a SOC 2 Report that will include the results of your audit. The report will give an overview of the security controls you have in place and how these align with SOC 2 requirements. This report will be shared with prospects, customers, and partners who request it.
What are the SOC 2 Compliance Requirements?
SOC 2 differs from other compliance standards. SOC 2 is not a checklist of controls that you must implement. Instead, it takes a risk-based approach to presenting business problems and the broad circumstances for which you will need to find solutions. Instead of telling you to install firewalls to secure your data, the report says: "The assessment and risk of fraud includes consideration of threats, vulnerabilities, and other risks that are specifically related to IT and accessing information."
The SOC 2 criteria are broad, and therefore, each organization will have a different way of implementing its SOC 2 controls. You will create security practices and controls that are suitable for your company as you work towards SOC 2 compliance.
Trust Services Criteria - 101
SOC 2 is based on five Trust Services Criteria. Your auditor will evaluate your infrastructure and your verified security practices in relation to these criteria.
The five TSC include security, privacy and confidentiality, as well as processing integrity and availability. Security criteria (also called common criteria) are controls required for all SOC 2 Reports. Only the four other categories need to be considered if they apply to your company's operations. If your company does not process data for your customers, then processing integrity will not be included in your SOC 2 Report.
Take a closer look at each TSC Category and its role in SOC 2 requirements.
The Security of Your Own Home
SOC 2 is built on the security criteria. The security criteria include more than 30 controls, which must be met by any organization wishing to achieve SOC 2. This category is designed to protect both your organization's and customers' data from unauthorized access.
Examples of security criteria include
- CC2.2: The entity communicates internally information, including objectives and responsibilities of internal controls, which is necessary to support internal control.
- CC3.2: The entity identifies and analyses risks that could prevent the achievement of the objectives within the entity. This analysis is used to determine how risks should be handled.
- CC6.1: To meet its objectives, the entity implements logical-access security software, infrastructures, and architectures to protect information assets from security incidents.
Availability
Employees and customers who need your data for a specific purpose will need consistent access. This principle ensures that your data will be available for the intended purpose and can be recovered if there is a technical problem or data breach.
Examples of availability criteria include
- A1.1: The entity monitors and evaluates its current processing capacity, including the use of infrastructure, data, and software, to meet capacity demands and implement additional capacity.
- A1.3: The entity tests recovery plans and procedures to support system recovery to achieve its objectives.
Confidentiality
You may have to include confidentiality as part of your SOC 2 if your organization handles confidential data such as your customers' business secrets, intellectual properties, or personal details. This category contains controls that ensure data is only accessible by authorized people.
These criteria include
- C1.1: To meet its confidentiality objectives, the entity must identify and maintain confidential information.
- C1.2: The entity uses confidential information to achieve the entity's confidentiality objectives.
Processing Integrity
You'll also need to include controls for processing integrity in your SOC 2 if you process data for your customers. This category includes data manipulation, such as running calculations or analytics. This category will ensure that your customers receive accurate information and calculations.
Process Integrity includes criteria like:
- PI1.1: To support the use and benefit from products and services, the entity acquires or creates quality information, communicates it, and uses it to achieve the processing objectives, including the definition of the data processed, product and service specifications, and the description of the product.
- PI1.2: This entity implements policies, procedures, and controls to ensure that system inputs are complete and accurate, resulting in the production of products, services, and reports to meet its objectives.
- PI1.3: This entity uses policies and procedures to process the system to produce products, services, and reports that meet its objectives.
You Can Also Find Out More About Privacy
Privacy criteria give consumers control over how their data is collected and used. This includes providing information about data collection, ensuring that consent is given, and asking for the deletion of their data.
Some example privacy criteria include:
- P1.1: The entity notifies data subjects of its privacy practices to achieve the privacy objectives. To meet privacy objectives, the notice is updated in a timely fashion and sent to data subjects.
- P2.1: The entity informs the data subject of the choices they have regarding the collection, usage, retention, disclosure, and disposal of their personal information, as well as the possible consequences of those choices.
SOC 2 Types 1 and 2 Requirements
SOC 2 reports are divided into two categories: SOC 2 type 1 and SOC 2 type 2. A SOC 2 Type 1 report analyses your controls at one point in time, while a SOC 2 Type 2 tests your controls and monitors them over time to determine their effectiveness.
Both types of reports have the same requirements and controls, but a SOC2 Type 2 audit can provide greater insight into how effective your controls are.
Start your SOC 2
It takes an average SOC 2 process about a year to complete, from the time you begin preparing your controls until you receive a finished SOC 2 report. You'll have to scope out your SOC 2 according to the TSCs that apply to you. Then, you will need to set up and test the controls, gather evidence, then find an auditor. Compliance automation can reduce this time by half.
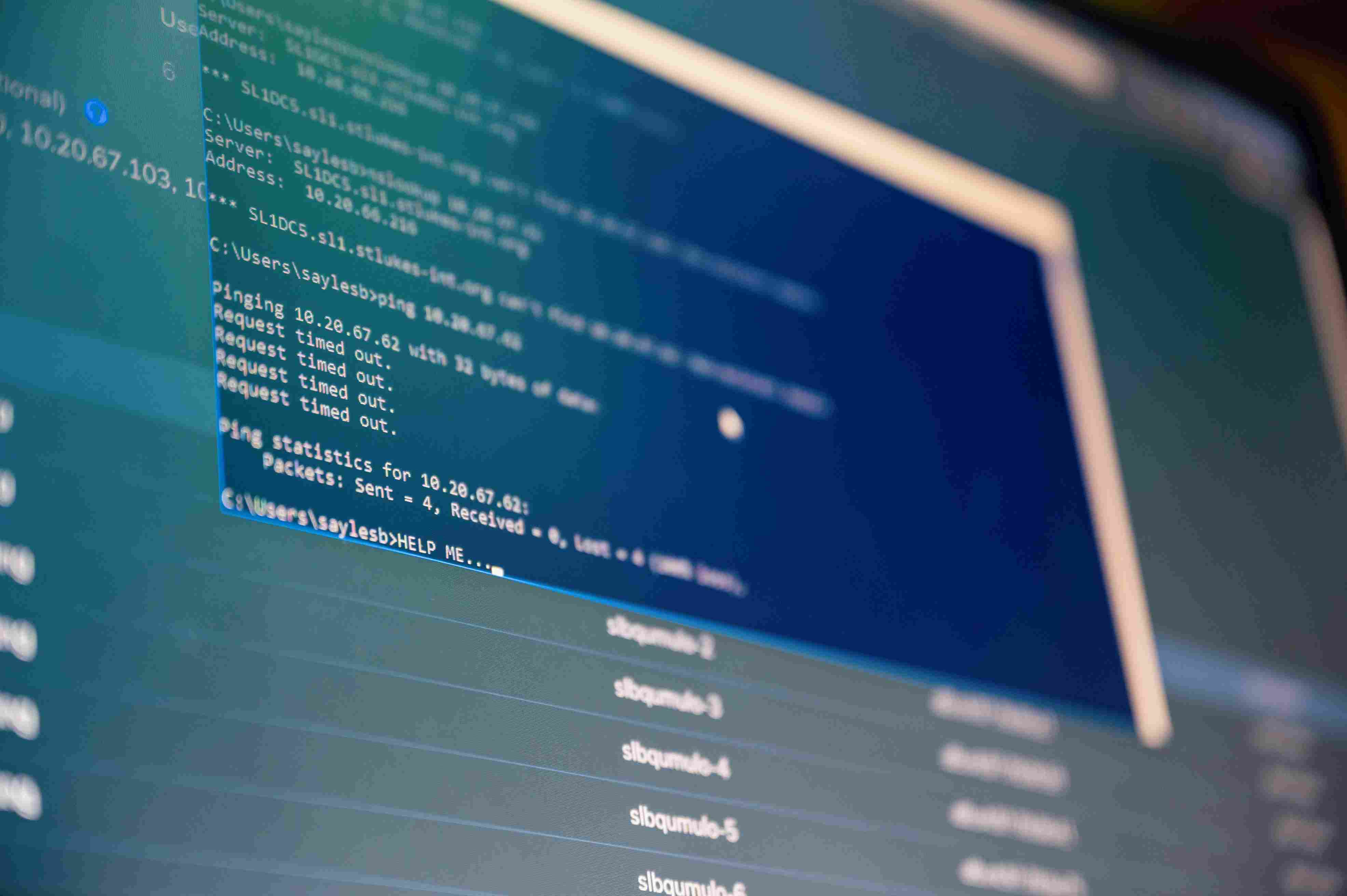
Sentant’s trust management platform can help you streamline your SOC 2: Here's an example of an automated SOC2:
- Connect your infrastructure using our 200+ integrations.
- One unified view to assess your risk
- Identify non-compliance areas.
- Automate the collection of evidence and centralize your documents.
- Find an auditor who has been Sentant-vetted within the platform.
- Completing your SOC 2 will take you half the time.
Conclusion
SOC 2 compliance is more than a certification—it’s a public statement of your company’s dedication to security, privacy, and customer trust. While the process may seem daunting, technology and expert guidance make it achievable for businesses of any size.
At Sentant, we simplify SOC 2 from start to finish. Our automation-driven platform handles integrations, evidence collection, and auditor connections—all from one place. Whether you’re preparing for your first SOC 2 audit or maintaining ongoing compliance, Sentant helps you get certified faster and stay compliant effortlessly.
Contact Sentant today to schedule a free demo—and discover how our platform can cut your SOC 2 compliance time in half while strengthening your security posture.
Frequently Asked Questions
1. What is SOC 2 compliance, and why does it matter?
SOC 2 compliance verifies that your organization has the right controls to protect customer data. It’s not just a technical requirement—it’s a key trust signal for clients, investors, and partners who want assurance that their data is safe with you.
2. How long does it take to achieve SOC 2 compliance?
The process typically takes 9–12 months, depending on your current security maturity and audit scope. Using compliance automation tools like Sentant can reduce that timeline by up to 50%.
3. What’s the difference between SOC 2 Type 1 and Type 2 reports?
A Type 1 report assesses your controls at a single point in time, while a Type 2 report evaluates how well those controls perform over several months. Type 2 provides stronger proof of reliability for customers and partners.
4. Does my company need all five Trust Services Criteria?
Not necessarily. Only Security is mandatory. The other four—Availability, Confidentiality, Processing Integrity, and Privacy—are included based on your operations and how you handle customer data.
5. How does Sentant make SOC 2 compliance easier?
Sentant automates the hardest parts of SOC 2 preparation. It integrates with your systems, collects audit evidence automatically, identifies compliance gaps, and connects you with vetted auditors—all through one secure platform. The result? Less stress, faster audits, and stronger customer trust.
Will Pizzano, CISM is Founder of Sentant, a managed security and IT services provider that has helped dozens of companies achieve SOC 2 compliance. If you’re interested in help obtaining SOC 2 compliance, contact us.