Managed IT Services
Managed IT services allow startups to scale faster by offloading IT tasks like device management, security, compliance, and onboarding to a specialized provider, freeing founders to focus on growth. They offer predictable costs, elastic capacity, and proactive monitoring to reduce outages while providing built-in security and compliance support from the start. This flexible model ensures smooth onboarding, standardized systems, and stronger resilience—helping startups stay productive and secure without building a full IT department too early.
How Managed IT Services Help Startups Scale Faster
Growing fast is exciting—until devices, logins, tickets, and security eat your week. Managed IT services pull that weight so you can ship product, close deals, and serve customers without tech slowdowns.
What “Managed IT” Actually Covers
You can switch on a managed IT provider (MSP) and get a ready-made stack:
- Help desk via chat/email/phone with clear SLAs
- Device management (MDM): standardized laptop/phone setup, encryption, remote wipe
- Identity & access: SSO (Okta/Azure AD/Google), MFA, role-based access, offboarding
- Cloud operations: backups, monitoring, patching, incident response, change control
- Network & endpoint security: Wi-Fi/VPN, EDR/antivirus, web filtering, vulnerability scans
- Compliance support: policy templates, evidence gathering, access reviews (SOC 2/ISO/GDPR)
You choose the pieces you need now and add more as you grow.
Why It Helps You Scale—Fast
1) Elastic capacity. Instead of hiring a whole IT team, you tap a bench of specialists. Add or remove seats as hiring waves come and go.
2) Predictable costs. Most MSPs price per user or device. You forecast spending and avoid surprise invoices for “emergencies.”
3) Faster onboarding. Day-one laptops, accounts, and permissions mean new hires produce work, not tickets.
4) Fewer outages. So proactive monitoring, a reliable patch rhythm, and well-rehearsed backups all help reduce the dependency on fire-fighting and late-night pings.
5) Built-in security. MFA, disk encryption, EDR, and network segmentation lower risk as your customer data and profile grow.
A Week-In-The-Life Example
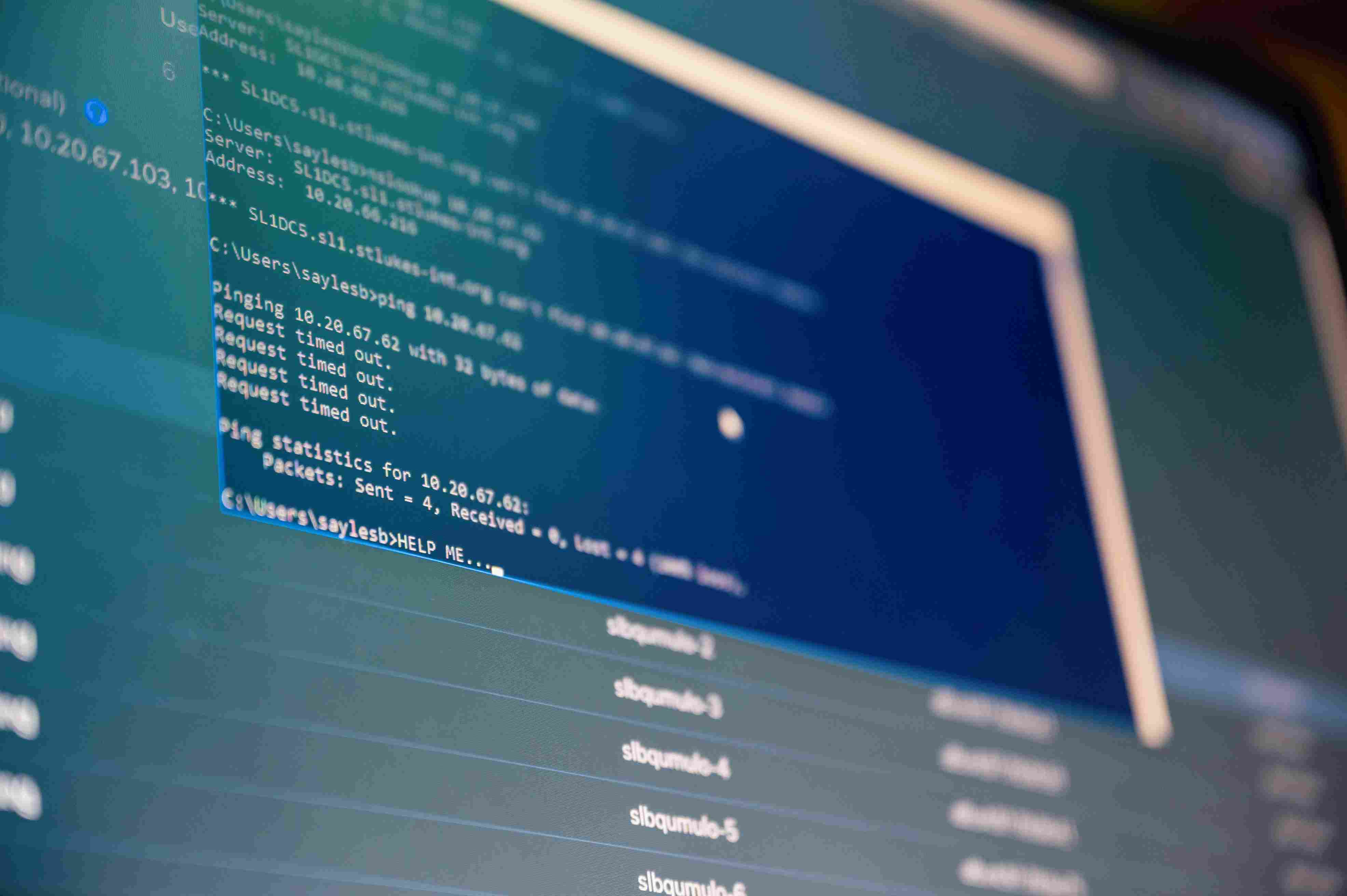
You’re hiring 12 people next month—six SDRs, four engineers, two customer success managers.
- Two weeks out: Your MSP orders/imagines laptops, defines SSO groups, and maps access (CRM, code repo, support tools).
- One week out: Devices are onboarded to MDM with baseline configuration (encryption on, firewall on, EDR installed). Accounts are provisioned, and least privilege is granted.
- Day one: New hires unbox, sign in, and receive a brief orientation from the help desk.
- Week one: Ticket patterns are tracked; your MSP tunes automation and knowledge base articles to reduce repeats.
Managers focus on training and targets—not tech setup.
Cost Control Without the Drag
- Avoid big up-front spend. Skip building a full internal IT stack before you need it.
- Enable advanced capability only when necessary. SIEM, vulnerability scanning, DLP, or mobile device controls can start as light and grow with sales and security reviews.
- One accountable partner. Instead of managing five suppliers, you have one SLA, one dashboard, and one route to escalation.
Security and Compliance From the Start
As traction brings bigger customers, expectations rise.
Security baseline
- MFA everywhere, not just email
- Full-disk encryption on all laptops
- EDR with alerting and response playbooks
- Standardized patch windows and change approvals
- Phishing simulations and short security training
Resilience
- Recovery time (RTO) and recovery point (RPO) targets agreed and tested
- Backups with periodic restore drills
- Incident response plan with roles, communications, and after-action reviews
Compliance
- Policy library mapped to your frameworks (SOC 2/ISO 27001/GDPR/HIPAA)
- Evidence collection (access reviews, backup logs, change tickets) streamlined
- Vendor security reviews and data-processing agreements coordinated
This foundation shortens security questionnaires and keeps enterprise deals moving.
Productivity You Can Feel
- Less context switching. Engineers and PMs spend fewer hours on “quick IT favors.”
- Clear response times. A ticketing portal and SLA set expectations and reduce frustration.
- Standardized environments. Fewer “works on my machine” moments when everyone has the same baseline images and access.
Common Concerns (And Quick Answers)
“We’ll lose control.” You retain admin rights and visibility; the MSP operates day-to-day under agreed-upon guardrails and change approvals.
“We’re too small.” Even a 10-person team benefits from SSO, backups, and a real help desk. Start minimal and expand.
“It’s pricey.” Compared to one FTE plus tools, training, 24/7 coverage, and the cost of downtime, MSPs spread those costs across clients.
How to Choose the Right Provider
- Stage and stack fit. Look for startups at your size using your platforms (Google/Microsoft, AWS/Azure/GCP).
- Security first. MFA by default, device encryption, EDR, patch SLAs, tested restores, and a written incident plan.
- SLA clarity. Response and resolution targets, escalation paths, and after-hours coverage are clearly documented.
- Compliance help. Ability to map controls to SOC 2/ISO/GDPR and provide evidence packs.
- Transparent pricing. Per-user/device pricing, straightforward project rates, and a change-management process.
- References. Ask for two: one company at your stage and one a stage ahead.
Implementation Playbook (Simple and Fast)
- Baseline audit (1–2 weeks). Inventory devices, accounts, apps, and risks.
- Quick wins (first month). Turn on MFA, enroll devices in MDM, standardize laptop images, and enable backups.
- Access hygiene. Map roles and groups; enforce least-privilege and an offboarding checklist.
- Monitoring & patching. Define windows, approvals, and rollback steps.
- Security awareness. Short welcome course and quarterly refreshers; lightweight phishing tests.
- Compliance runway. Draft policies, start collecting evidence, and schedule mock audits if needed.
- Review rhythm. Monthly ops review and a quarterly roadmap checkpoint tied to hiring, new products, and customer demands.
When to Bring It In-House
Most startups run lean with an MSP until one of these happens:
- You need daily on-site support (labs, hardware-heavy teams).
- You reach 150–250 employees and want embedded IT at each office.
- Your product has a complex infrastructure that demands a dedicated internal platform/IT blend.
Even then, many keep the MSP for after-hours coverage, compliance tooling, and escalations.
Bottom Line
Managed IT turns scaling from “hold it together” to “we’ve got this.” You get a steadier platform, faster onboarding, stronger security, and clear costs—without having to build a whole IT department too early. That means more time for creating a product and winning customers.
Scaling a startup is hard enough without worrying about IT headaches. At Sentant, we specialize in helping high-growth companies stay secure, compliant, and productive with flexible managed IT services tailored to your stage. Whether you’re onboarding your first hires or preparing for enterprise audits, our team gives you the tools and support to move faster with confidence.
Contact Sentant today to see how we can help your startup scale smarter and safer.
FAQ
How fast can a provider scale with us?
Once your baseline is in place, adding users and devices is routine—often within hours to a couple of days for larger waves.
Are managed IT services only for tech companies?
No. If your team uses laptops, cloud apps, or customer data, you’ll benefit—SaaS, ecommerce, finance, healthcare, nonprofits.
Will they handle cloud migrations?
Many do. Ask about your cloud (AWS/Azure/GCP), their migration plan, testing, and rollback steps before cutover.
How do they protect data privacy?
By enforcing MFA, encryption, least-privilege access, backups with restore tests, vendor reviews, and controls mapped to the privacy laws you face.
What should I ask during the evaluation?
“Show me your standard laptop image, your incident playbook, last restore test results, and two startup references.”
Will Pizzano, CISM is Founder of Sentant, a managed security and IT services provider that has helped dozens of companies achieve SOC 2 compliance. If you’re interested in help obtaining SOC 2 compliance, contact us.