zero-trust architecture
This guide explains why startups should move from traditional VPNs to Zero-Trust Architecture (ZTA) to improve security and scalability. Unlike VPNs that grant broad access once logged in, Zero-Trust continuously verifies users and devices, limits access with least-privilege rules, and prevents hackers from moving across systems if credentials are compromised. By adopting a phased transition to Zero-Trust, startups can enhance security, support remote teams, simplify compliance, and maintain productivity without the limitations of outdated VPN setups.

Moving Your Startup From VPN to a Zero-Trust Architecture
When you are at the stage of scaling a startup, by now, it should be easy to understand that speed is king. On the other hand, an obsolete security infrastructure is a huge lead weight. The days of wrapping a legacy VPN around your company’s crown jewels feels like trying to protect a modern glass skyscraper with a medieval moat. The old VPN mentality that is damaging modern teams. Most importantly, we’ll discuss how Zero-Trust Architecture (ZTA) provides a human-centric and scalable approach for keeping your distributed workforce secure
Key Takeaways
- Verification is the New Normal: Zero-Trust operates on a simple, slightly paranoid idea: every connection attempt is a potential threat. The system mandates rigorous identity and device health checks for every single user request, every single time.
- Contain the Damage: By ditching the "all-access" nature of a traditional VPN, you stop hackers from jumping between your internal systems. This effectively limits the "blast radius" if an employee’s credentials ever get swiped
- Frictionless Productivity: Modern Zero-Trust tools get rid of those annoying login clients and constant connection drops that kill your team's momentum. Your people stay in their flow state while data remains tucked behind invisible shields.
- Fast-Track Your Compliance: Moving to this framework makes the grueling road to SOC 2 or ISO 27001 much less painful. It proves to enterprise customers that your startup handles data with adult-level maturity.
What Is Zero-Trust Architecture?
At its most basic, Zero-Trust is a security model based on a single tenet: “Never trust, always verify.”
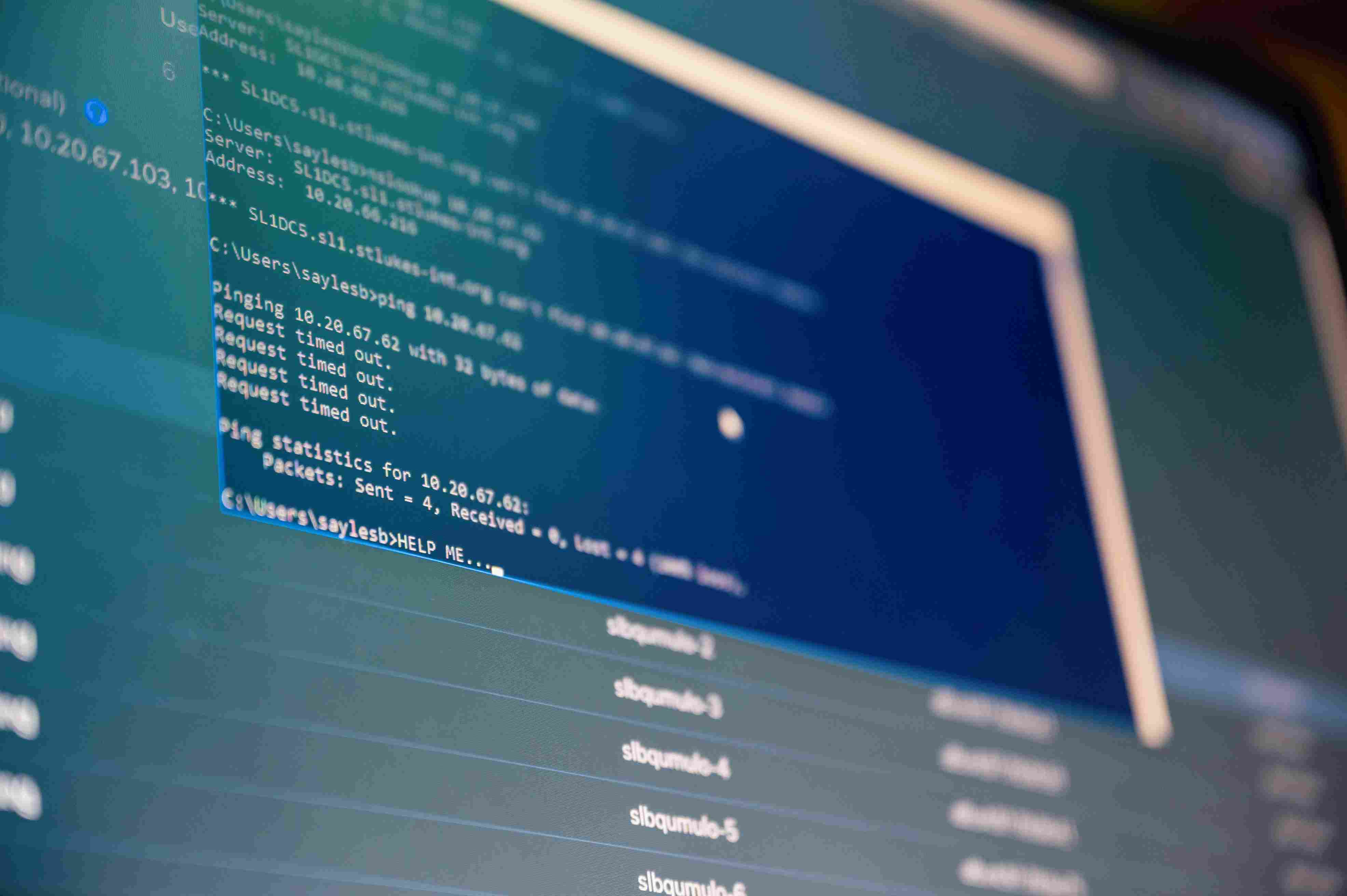
Security is a castle, in the old days. Set up a drawbridge (VPN), and once someone is over the drawbridge they trust them to race around the halls. In a Zero-Trust world, there are no halls — only locked doors. You were within the building may be, when you want to open a new door, ID verification is needed every time
- The 'Never Trust' Directive: Whether a request originates from the office printer or from the CEO's laptop, each connection is classified as a threat — or breach — until proven otherwise.
- Continuous Validation: If you are logged in at 9 A.M. does not imply that you are safe at 10 A.M. Architecture that keeps checking out if your device security posture has changed.
- Built to a Zero-Trust model, Micro-Perimeters: Rather than one process corral around your business, we place small, virtually imperceptible fences around every app, database, and file on the network.
- Contextual Intelligence: The system understands the who, what, where, and when. So, for example, it could let a dev in from their home office but deny them if they attempt to log on at 3:00 AM from some unnaturally suspicious IP address.
Why is Zero-Trust the Ultimate Survival Strategy for Startups?
When you’re running a startup, you’re a high-value target with a limited security budget. You’re likely remote-first, using dozens of SaaS tools, and hiring contractors at a record pace. A traditional VPN simply wasn't built for this kind of "organized chaos."
- Killing Lateral Movement: In a typical breach, a hacker steals one junior employee's login and "hops" through the network until they find the production database. Zero-Trust stops those hops; the hacker stays trapped in the one minor room they broke into.
- Solving the "BYOD" Headache: Most startups let employees use their own gear. Zero-Trust allows you to secure the data inside the apps without needing to take "Big Brother" levels of control over your employees' personal devices.
- Scaling Without the Friction: VPNs tend to break as you add more users. In contrast, Zero-Trust is cloud-native. Whether you have 5 employees or 500, the security process stays exactly the same
- Closing the "Trust Gap" with Big Tech: If you want to sell to a bank or a healthcare giant, they will grill you on security. Being able to say, "We run a full Zero-Trust Architecture," is a massive green flag that can cut weeks off your sales cycle.
- Eliminating VPN Fatigue: Let’s be real: your engineers hate VPNs. They’re slow, and they disconnect. Zero-Trust is largely invisible, which means your team will actually use it instead of looking for risky workarounds.
The Core Pillars: How Zero-Trust Operates in the Wild
Building a Zero-Trust Architecture isn't about buying a single "magic" app; it’s about weaving together a few common-sense security habits.
- Identity is the New Perimeter: Your Identity Provider (IdP), like Okta or Google, becomes the heart of your security. If an employee moves on or an account looks "wonky," you can kill their access across every platform with one click.
- Checking Device Health: It’s not just about who is logging in, but what they are using. Your policy might allow access from a managed company laptop but block a personal tablet that hasn't been updated in years.
- The Rule of Least Privilege: This is the "Need to Know" basis for the digital age. A marketing hire shouldn't even be able to see the production servers. Limiting access to the bare essentials ensures a small mistake doesn't turn into a catastrophe.
Real-World Applications for High-Growth Teams
You might wonder how this actually changes the daily vibe of your office. The benefits are immediate and practical.
- Securing Your Remote Culture: Since your team is distributed, Zero-Trust ensures a home Wi-Fi router isn't a backdoor for attackers. Every request is verified regardless of the network.
- Managing Contractors and Freelancers: Startups lean on outside help. Instead of giving a contractor a VPN login that reveals your whole world, you can give them access only to a specific Figma board or a single repo.
- Smoothing Out Due Diligence: When you head into an acquisition, investors will hunt for "Security Debt." Having a Zero-Trust setup shows you’re a mature organization, which can seriously help your valuation.
The Migration Roadmap: Moving From Moats to Micro-Perimeters
Switching over doesn't need to be a weekend-ruining project. In fact, trying to flip a switch all at once is a great way to break your team’s workflow. Instead, try a phased rollout:
- Identify the "Crown Jewels": Usually the production environment or customer database. Put an Identity-Aware Proxy (IAP) in front of these first.
- Verify Hardware: Start requiring basic device management so you know the hardware is safe.
- Phase Out the VPN: Once high-stakes assets are covered, slowly turn off the VPN for smaller internal tools. You’ll build security "muscle memory" without a productivity meltdown.
How Sentant Facilitates the Zero-Trust Shift
At Sentant, we’ve watched a lot of startups get stuck in the "VPN trap." We specialize in helping you tear down that medieval moat and replace it with a sleek, modern Zero-Trust Architecture. Rather than just tossing a list of software at you, we act as your fractional security partners.
We help you pick the right Identity Provider, set up your device rules, and build a network where your engineers stay fast, and your data stays hidden. Our mission is to turn your security into a selling point.
Conclusion
The "Castle-and-Moat" era is officially in the rearview mirror. For any startup that wants to thrive in 2026, the VPN is a single point of failure that’s both risky and annoying. By embracing Zero-Trust, you’re moving toward a smarter future where identity is your real shield. This shift doesn't just lock the doors; it gives your team the freedom to work safely from anywhere on the planet.
Frequently Asked Questions
Is Zero-Trust Architecture too expensive for an early-stage startup?
Not at all. You’re likely already paying for tools like Google Workspace or AWS that have these features built in. The cost of a single breach is infinitely higher than the monthly sub for a solid identity provider.
Does this mean my team has to deal with MFA for every single click?
No. Zero-Trust is actually smarter than that. If you're on your usual laptop in your usual city, it stays out of your way. If you suddenly try to log in from a new device in a different country, that’s when it asks for extra verification.
Can we keep our VPN for a few legacy things while we switch?
Yes. Most startups run a "Hybrid" model during the move. You might keep the VPN for one old internal server while moving all your modern SaaS and cloud tools over to the Zero-Trust framework.
How exactly does Zero-Trust help with SOC 2 audits?
It makes the paper trail a dream. SOC 2 is all about proving who has access to what. Because Zero-Trust tracks every access request in a central log, you can give your auditor a clean, automated report instead of hunting through spreadsheets.
Do I need a massive IT department to run this?
Actually, it’s often easier than managing a VPN. You don't have to patch hardware or mess with complex firewall rules. You manage everything from a central dashboard, fitting perfectly with how modern DevOps teams already work.
Will Pizzano, CISM is Founder of Sentant, a managed security and IT services provider that has helped dozens of companies achieve SOC 2 compliance. If you’re interested in help obtaining SOC 2 compliance, contact us.