Cybersecurity: What Startups Should Know
Cybersecurity is critical for startups because they are common targets for cybercriminals due to valuable data and often weak security defenses. A single breach can cause severe financial losses, legal issues, and reputational damage that many startups cannot recover from. To reduce risks, startups should adopt proactive security practices such as two-factor authentication, encryption, regular backups, employee training, and a clear incident response plan.

Cybersecurity: What Startups Should Know
In the high-stakes world of the San Francisco, CA tech scene, a startup’s reputation is its only real currency. You can have the most disruptive code in the Valley, but if your perimeter is soft, you’re just a target waiting for a payday. Modern hacking isn't just some kid in a hoodie; it’s a globalized industry designed to strip-mine your data and leave your brand in the dirt.
Key Takeaways
- Target Profile: Startups are often preferred targets because they prioritize growth over "boring" defensive infrastructure.
- The 60% Rule: Most small businesses that suffer a major breach shutter their doors within six months of the incident.
- Human Element: Over half of all data leaks are the result of internal negligence, not sophisticated zero-day exploits.
- Proactive Defense: Security isn't a "set it and forget it" tool; it’s a living culture of encryption, backups, and hygiene.
Why is cybercrime a lethal threat to small businesses?
Smaller companies are prime targets because they lack the battle-tested experience required to fend off global hacking syndicates. While a giant like Google has an army of engineers, a lean startup in San Francisco, CA, often has a "security posture" that is effectively nonexistent. When you're burning cash to scale, defense feels like a luxury—until a ransomware demand hits your inbox.
According to the Ponemon Institute, global attacks against SMBs are skyrocketing. Nearly 45% of surveyed firms admitted their security was ineffective, and 39% had zero plan for when—not if—the walls come down. In the Bay Area, where first impressions dictate your next funding round, a breach is a death sentence. A legacy brand might survive a PR hit, but a startup hasn’t built enough consumer trust to weather a total data exposure. Look at the Target breach: 140 lawsuits and a fired CEO. For a startup, that same pressure just results in a "Closed" sign.
What are the real-world consequences of a hack?
The fallout of a breach is a domino effect of lost revenue, destroyed investor confidence, and crippling legal fees. Take the case of Rokenbok; they lost thousands in sales because hackers held their engineering data for ransom. It’s a recurring nightmare for those who don't patch the holes. When your database gets hit with malware, the clock starts ticking against your survival.
The Strategic Framework: Building a Defensible Perimeter
- Immediate Containment: Seal the leak the second a red flag appears.
- Kill active sessions and restrict compromised devices immediately.
- Audit third-party app permissions that employees frequently grant without reading.
- Regulatory Triage: Navigate the legal minefield before the fines mount.
- File breach notices with the relevant agencies to stay compliant.
- Consult with counsel to understand your liability under California data laws.
- Offensive Validation: Don't guess if you're safe—know it.
- Hire a specialist for penetration testing to find the "open windows" in your code.
- Implement an incident response plan that every founder knows by heart.
Multi-Layered Entity Bullets
- Penetration Testing: A simulated "ethical" attack to find vulnerabilities before the bad guys do.
- 2FA (Two-Factor Authentication): A mandatory second layer of identity verification that stops 99% of bulk bot attacks.
- End-to-End Encryption: Scrambling data so it’s useless to a thief, even if they manage to intercept it.
- Ransomware: Malicious software that locks your files until you pay a (usually untraceable) fee.
Expert Perspective: The "Coffee Shop" Liability
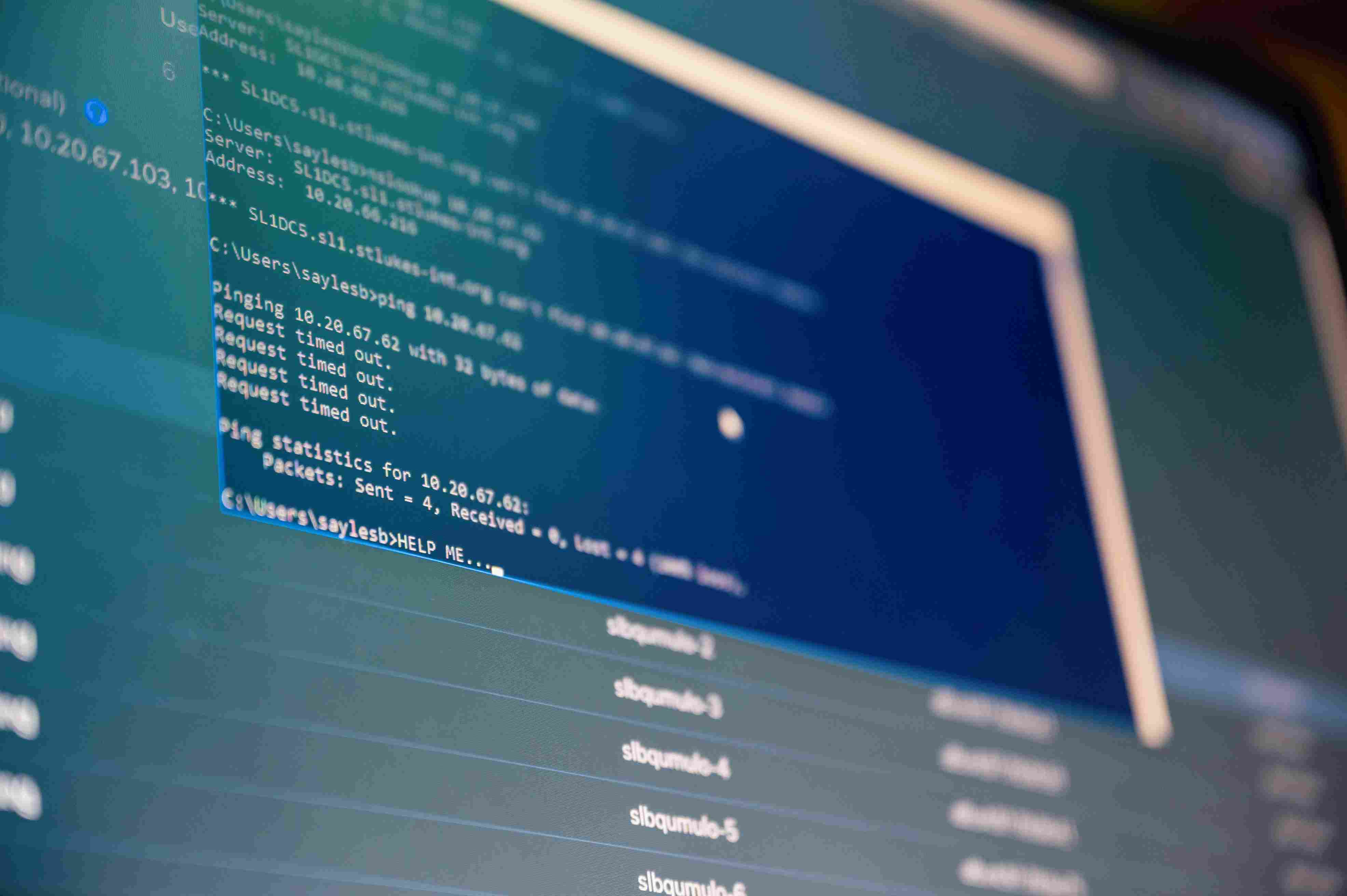
Here is the gritty reality: Your biggest threat isn't a Russian botnet; it's your lead dev using the airport WiFi to check the production server. I've seen entire companies compromised because of one "convenient" login. Use a dedicated business phone for your team. It centralizes communication under IT control, allowing you to revoke access the moment a device is lost or an employee moves on.
How should your business respond to a breach?
Speed is the only thing that saves your reputation when the servers go dark. You cannot pull a Yahoo and wait years to tell your customers they’ve been exposed. You have to move fast. Notify the victims, call in the experts, and stop the bleeding by restricting the compromised hardware. Cybersecurity: what startups should know is that transparency—while painful—is the only way to retain the trust of your San Francisco user base.
Best Practices for Startup Survival
- Audit social footprints: Keep personal pet names and kids' birthdays off LinkedIn to prevent social engineering.
- Centralize with tools: Use web application firewalls and SSL certificates to create a unified defense.
- Write the policy: If the plan isn't on paper, it doesn't exist during a crisis.
- Update the "POS": Don't be like Wendy’s; outdated point-of-sale systems are a magnet for credit card thieves.
- Wipe and Restore: Keep off-site, encrypted backups so you can laugh at a ransomware demand.
- Hire the Grunts: Outsource the heavy lifting to experts who live and breathe threat vectors.
Mastering the Future of Startup Defense
The reality is that hackers don't discriminate, but they definitely have a preference for the "low-hanging fruit" of the startup world. Moving fast and breaking things is a great mantra for development, but it's a disaster for security. Treat your defense as a core feature of your product, not a patch you'll apply "later."
- Identify your most sensitive data silos today.
- Enforce 2FA across every single corporate account.
- Book a demo to schedule a deep-dive audit on cybersecurity: what startups should know.
Visit Sentant website for more information.
Frequently Asked Questions
Why are startups specifically targeted by hackers?
Hackers target startups because these companies often possess valuable intellectual property but lack the robust security budgets of enterprises. This creates a "high reward, low effort" scenario for cybercriminals looking for an easy entry point.
How much does a typical data breach cost a small company?
Beyond the immediate technical recovery, costs include legal fees, regulatory fines, and lost customer lifetime value. For many startups, the cost is total, leading to business closure within six months of the initial attack.
Is cloud storage safer for my startup's data?
Cloud storage can be safer, but only if configured correctly. Misconfigured "S3 buckets" or weak access credentials are common ways that sensitive startup data ends up exposed on the public internet.
What is the most common way hackers get into a system?
Phishing and human error remain the top entry points. Hackers exploit employee negligence, such as weak passwords or clicking on malicious links, to bypass even the most expensive firewall software.
Should I pay the ransom if my data is encrypted?
Most experts advise against paying. There is no guarantee you will get your data back, and paying often marks your startup as a "soft target" for future attacks by the same group.
Will Pizzano, CISM is Founder of Sentant, a managed security and IT services provider that has helped dozens of companies achieve SOC 2 compliance. If you’re interested in help obtaining SOC 2 compliance, contact us.