Cybersecurity Services for Healthcare in Los Angeles
Cybersecurity services for healthcare in Los Angeles are essential to protect sensitive patient data, maintain operations, and meet strict regulations like HIPAA. Medical organizations face constant threats such as ransomware and phishing, requiring advanced solutions like 24/7 monitoring, encryption, multi-factor authentication, and secure backups. By using managed security services, providers can reduce risk, ensure compliance, and focus on patient care while experts handle ongoing protection and threat response.

The Definitive Guide to Cybersecurity Services for Healthcare in Los Angeles
In the sprawling medical landscape of Southern California, your digital infrastructure is under constant siege. Healthcare organizations manage high-stakes patient data every hour, making cybersecurity services for healthcare in Los Angeles a non-negotiable line of defense for modern providers. From the high-traffic corridors of Cedar-Sinai to private practices in Santa Monica, the threat of a data breach isn't a "maybe"—it’s a matter of when.
Key Takeaways
- High-Value Targets: Patient records fetch premium prices on the dark web, making LA clinics prime targets.
- Operational Continuity: A ransomware attack doesn't just leak data; it halts life-saving patient care.
- Regulatory Teeth: HIPAA violations in California carry massive financial and reputational penalties.
- Proactive Defenses: Moving beyond basic firewalls to 24/7 managed detection and response is the new standard.
What Are the Core Cybersecurity Services for Healthcare in Los Angeles?
Cybersecurity services for healthcare in los angeles include a multi-layered defense strategy featuring real-time threat monitoring, advanced data encryption, and immutable backups. These solutions are specifically engineered to safeguard Electronic Health Records (EHR) and ensure that medical networks remain resilient against the sophisticated phishing and ransomware tactics currently targeting the Los Angeles medical community.
The Strategic Framework for Medical Data Security
- Phase 1: Perimeter Hardening
- Deploying Next-Gen Firewalls (NGFW) to scrub incoming traffic.
- Implementing Multi-Factor Authentication (MFA) across all provider portals.
- Phase 2: Active Threat Hunting
- Utilizing AI-driven Endpoint Detection and Response (EDR) to kill processes before they spread.
- Conducting regular vulnerability scans to patch the "cracks" in your software.
- Phase 3: Immutable Data Redundancy
- Creating "air-gapped" backups that hackers cannot reach or encrypt.
- Testing Disaster Recovery (DR) protocols to ensure a 4-hour return-to-service window.
Why Is the Los Angeles Healthcare Sector a Primary Target for Hackers?
Hackers aren't just looking for credit cards; they want the full "identity kit" found in medical files, which include social security numbers, histories, and insurance details. In a city like Los Angeles, where the density of specialized clinics is high, the attack surface is massive. If your systems go dark, the pressure to pay a ransom is immense because lives are literally on the line during a surgical schedule or a trauma intake.
How Do Managed Security Services Compare to In-House IT?

Which Specific Technical Protections Are Mandatory for HIPAA Compliance?
- AES-256 Encryption: The industry standard for locking down data at rest on your servers and in transit to other providers.
- Access Control Logs: A digital "paper trail" that records exactly who looked at a patient file and when.
- Secure Cloud Gateways: Protective tunnels for staff accessing patient data from home or a remote LA satellite office.
- Phishing Simulation: Training your front-desk staff to spot the "urgent" emails that are actually malware traps.
Expert Perspective: The "Grit" Factor
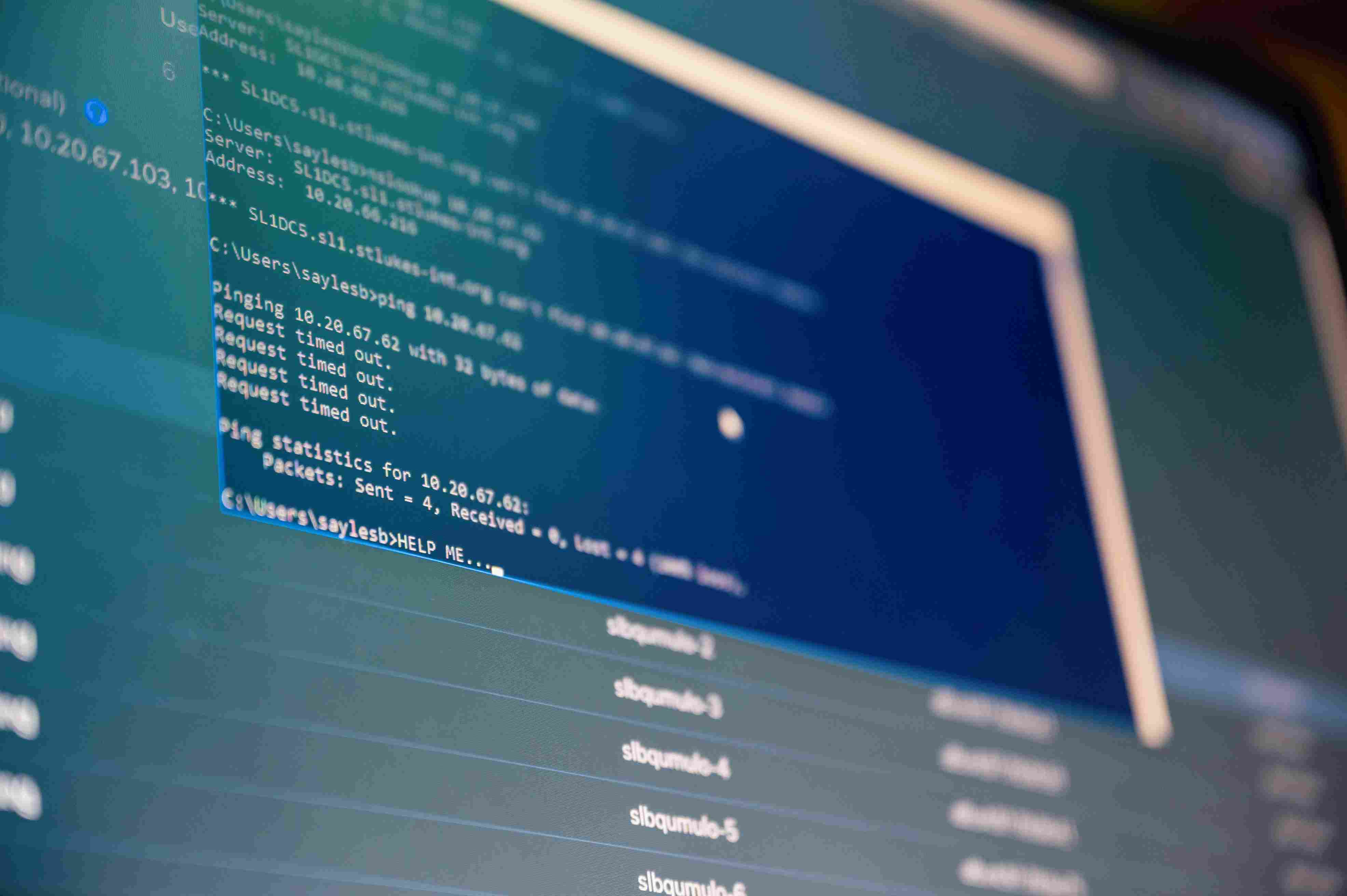
The Pro Tip: Most LA providers focus on the "front door," but the "back window" is usually left open. I'm talking about your networked medical devices—MRI machines, infusion pumps, and heart monitors. These often run on outdated operating systems. If you don't segment these devices onto their own private network, a hacker can hop from a guest Wi-Fi login straight into your surgical suite's hardware.
How Does Sentant Transform Your Medical Practice’s Security Posture?
At Sentant, we don't just sell software; we provide a "boots on the ground" defense for the complex Los Angeles medical environment. Our approach to cybersecurity services for healthcare in Los Angeles involves deep integration with your existing workflow to ensure security never becomes a bottleneck for patient care. We handle the heavy lifting of encryption and compliance so your team can focus on medicine.
- EHR (Electronic Health Records): The digital backbone of your practice that requires zero-trust access architecture.
- Managed Detection & Response (MDR): A proactive service that hunts for hidden threats 24/7.
- SOC 2 Compliance: A rigorous auditing procedure that proves your service provider handles data with elite security.
- Ransomware Remediation: The tactical plan used to scrub and restore systems if a breach ever occurs.
Putting Your Healthcare Strategy into Motion
Securing a medical practice in the modern age requires more than a prayer and an antivirus program. By leveraging professional cybersecurity services for healthcare in Los Angeles, you are making a commitment to your patients' privacy and your practice's longevity. Sentant stands ready to bridge the gap between complex medical technology and absolute digital safety.
Schedule your comprehensive security audit with Sentant today. Call now!
Frequently Asked Questions
Why is cybersecurity so critical for Los Angeles medical clinics?
It protects the integrity of patient care and prevents devastating financial losses from data breaches. In LA’s competitive market, a reputation for poor data handling can close a practice overnight.
What are the most common cyber threats facing healthcare today?
Phishing and ransomware are the top two. Attackers trick employees into clicking links or use exploits to lock your entire database until a bitcoin ransom is paid.
How much do professional security services cost for a mid-sized clinic?
Costs are typically based on the number of users and devices. Managed plans allow for predictable budgeting compared to the catastrophic $400k+ average cost of a single breach.
Can Sentant help with HIPAA and CCPA compliance audits?
Yes. We provide the technical documentation and security controls required to satisfy federal and state auditors, significantly reducing your legal liability.
How long does it take to deploy a full security framework?
Initial hardening can often happen within days. We prioritize high-risk gaps first—like backups and MFA—then move into long-term monitoring and staff training.
Will Pizzano, CISM is Founder of Sentant, a managed security and IT services provider that has helped dozens of companies achieve SOC 2 compliance. If you’re interested in help obtaining SOC 2 compliance, contact us.


.jpeg)