Startup IT Infrastructure
A strong startup IT infrastructure is essential for scaling efficiently, protecting data, and avoiding costly downtime as a company grows. By using cloud-first systems, standardized hardware, proactive security measures, and automated workflows, startups can improve collaboration, strengthen cybersecurity, and support rapid expansion without technical bottlenecks. Investing in reliable IT infrastructure early helps reduce technical debt, protect intellectual property, and keep teams productive as the business scales.

Building a Bulletproof Startup IT Infrastructure: The Founder’s Guide to Scaling Without the Crash
In the high-stakes ecosystem of San Francisco, CA, your tech stack is either your greatest accelerator or your heaviest anchor. Most founders treat their systems as an afterthought, only to realize—usually during a critical Series A pitch—that their foundation is made of glass. A robust startup IT infrastructure isn't just about having shiny laptops; it’s the structural integrity that allows your team to sprint without tripping over downtime, security breaches, or fragmented workflows.
Key Takeaways
- Stability is Scalability: Systems built for 5 people must be architected to handle 50 without a total teardown.
- Cloud-First Efficiency: Leverage decentralized environments to slash overhead and maintain a mobile, agile workforce.
- Security is Non-Negotiable: Implementing MFA and encrypted endpoints from day one prevents catastrophic data hemorrhaging.
- Frictionless Collaboration: Integrated toolsets eliminate "app fatigue" and keep communication lines clean.
- Proactive Maintenance: Solving a bottleneck before it stops production is the only way to protect your burn rate.
Why Is a Robust Startup IT Infrastructure Critical for Growth?
A dependable startup IT infrastructure acts as the nervous system of your business, ensuring that data flows and communication remains unbroken. In the competitive Bay Area market, where speed is the primary currency, you cannot afford the "death by a thousand cuts" that comes from sluggish networks or incompatible software. Investing in a professional-grade setup early protects your intellectual property and ensures that as your headcount explodes, your technology doesn't implode.
The Growth Strategy Framework
- The Audit Phase: Inventory every current SaaS subscription and hardware asset to identify redundant "shadow IT" costs.
- The Architecture Phase: Design a hub-and-spoke model where your central cloud identity (like Google Workspace or Azure) manages all peripheral apps.
- The Hardening Phase: Deploy enterprise-grade firewalls and endpoint protection to turn your remote fleet into a secure perimeter.
- The Automation Phase: Script your onboarding and offboarding processes so a new hire is ready to work in minutes, not days.
How Do You Choose the Right Hardware and Devices?
Selecting hardware requires a "buy once, cry once" mentality to ensure your team has the horsepower to execute without technical lag. Standardizing your fleet simplifies management and troubleshooting; if everyone is on the same build, a fix for one is a fix for all. Don't let a procurement manager talk you into "budget" rigs that will thermal-throttle and die inside of 18 months—your talent is too expensive to wait for a spinning rainbow wheel.
Why Are Cloud Services the Foundation of Modern Teams?
Cloud computing removes the physical limitations of a server room, allowing your startup IT infrastructure to live in the ether where it can scale infinitely. By shifting the heavy lifting to providers like AWS, GCP, or Azure, you trade massive capital expenditures for predictable operating costs. This shift is what allows a three-person team in a SoMa garage to wield the same computing power as a Fortune 500 company without the massive data center bill.
Technical Execution Entities
- Infrastructure as Code (IaC): Using tools like Terraform to manage your cloud environments through software.
- Zero-Trust Architecture: A security model that requires strict identity verification for every person and device trying to access resources.
- Managed Detection and Response (MDR): Outsourced security that hunts for threats across your network 24/7.
Expert Perspective: The "Shadow IT" Trap
The Pro Tip: Most startups leak 15-20% of their IT budget on "Zombie SaaS"—subscriptions signed up for by departed employees or forgotten pilots. Every quarter, run a "scrub" of your corporate card spend against your SSO logs. If a tool isn't being used by at least 80% of its seat count, cut it. Aggressive consolidation isn't just about saving cash; it’s about reducing your attack surface.
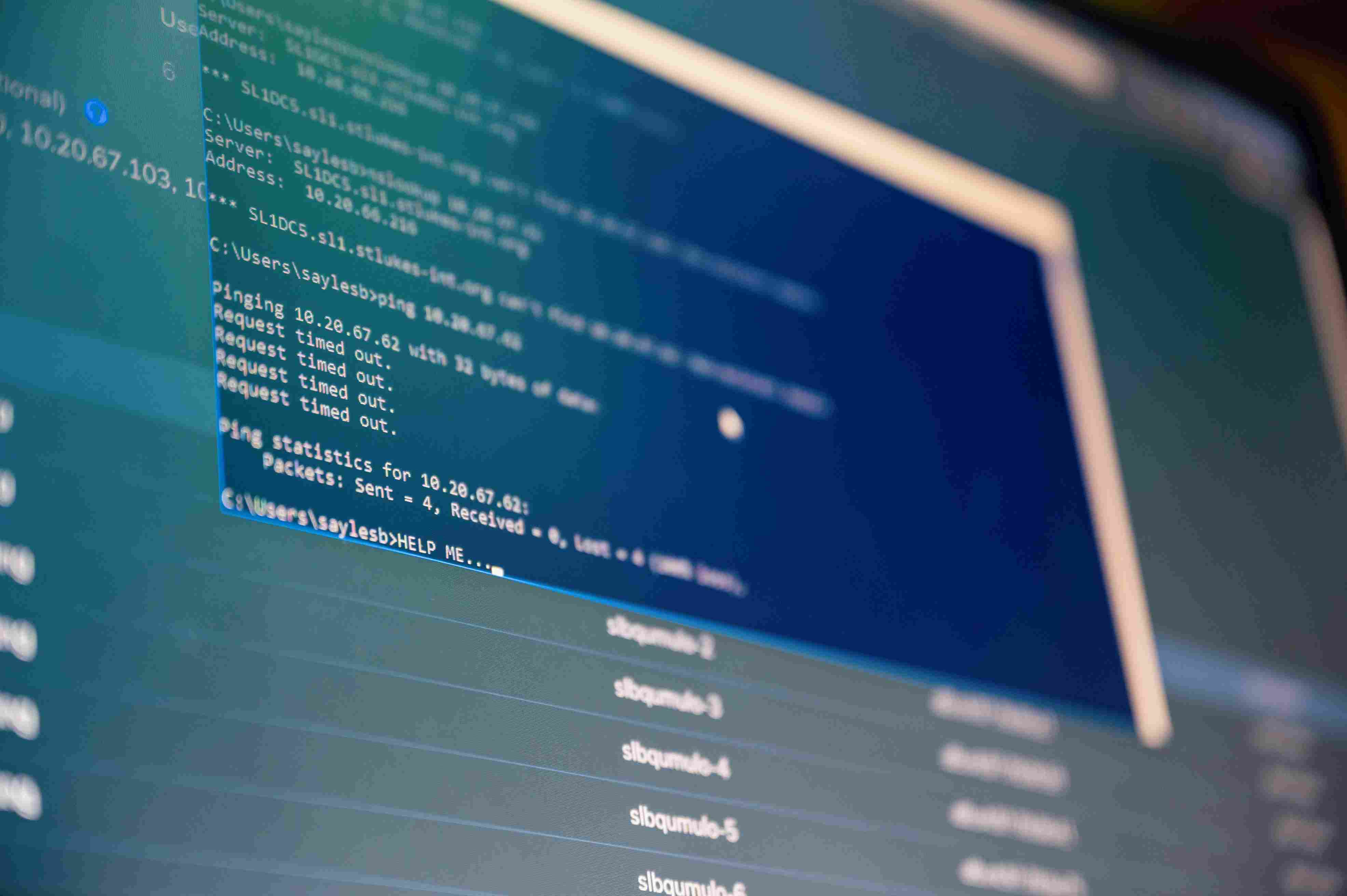
How Does a Secure Network System Protect Your IP?
Securing your network involves more than just a Wi-Fi password; it requires isolating guest traffic and encrypting every packet of data leaving the building. In an era of sophisticated phishing and man-in-the-middle attacks, your office network must be treated as a hostile environment. Utilizing VPNs for remote access and WPA3 encryption for on-site traffic ensures that your proprietary code and customer data don't end up on a dark-web marketplace.
Master Craftsman Requirements
- Hardened Firewalls: Deploying appliances that perform deep packet inspection to catch malware before it hits an endpoint.
- Segmented VLANs: Separating "Internet of Things" devices (like smart fridges or printers) from the production servers where the real work happens.
- Encrypted Tunnels: Mandating that all remote traffic flows through a secure gateway, regardless of whether the employee is at a coffee shop or their home.
Why Is Data Backup and Disaster Recovery Vital?
Disaster recovery is the insurance policy that ensures a single hardware failure or ransomware attack doesn't result in a permanent "game over" for your company. You need a 3-2-1 backup strategy: three copies of your data, on two different media, with one copy off-site (cloud). If your primary workspace is hit by a localized 4 p.m. Pasco County-style deluge or a Bay Area earthquake, your team should be back online within hours, not weeks.
Mastering the Future of Your IT Strategy
Building a world-class startup IT infrastructure isn't a one-time project; it’s a continuous evolution that mirrors your company's growth. By prioritizing security, cloud flexibility, and standardized hardware now, you eliminate the technical debt that kills most scaling efforts. The goal is simple: technology should be the invisible engine that drives your vision, never the bottleneck that stops it.
Ready to bulletproof your systems? Sentant specializes in building high-performance tech foundations for the next generation of industry leaders. Explore our deep-dive guide on startup IT infrastructure and learn how to secure your path to scale.
Frequently Asked Questions
Q: What are the biggest IT mistakes startups make?
A: The most common errors include ignoring security protocols to save time, purchasing consumer-grade hardware that fails under load, and failing to implement automated backups. These shortcuts create massive technical debt that becomes exponentially more expensive to fix as the team grows.
Q: When should a startup hire its first IT person?
A: Typically, once a company reaches 20–30 employees, the complexity of managing devices, permissions, and security exceeds what a founder or "tech-savvy" employee can handle. However, many startups choose to outsource this role earlier to specialized firms to maintain lean operations.
Q: How much should a startup budget for IT infrastructure?
A: A safe baseline is to budget approximately 4-7% of total revenue or a set "per-user" monthly fee for managed services and security. This investment covers the licensing, support, and hardware refreshes necessary to maintain peak productivity.
Q: Is cloud or on-premise better for a new company?
A: For 99% of modern startups, a cloud-first approach is superior due to its lower upfront costs, ease of remote access, and built-in scalability. On-premise servers are generally reserved for specialized industries with extreme data-sovereignty requirements or massive local processing needs.
Q: How does Sentant help with startup IT setup?
A: Sentant acts as a strategic partner, handling everything from initial network design and hardware procurement to ongoing cybersecurity monitoring and helpdesk support. We provide the expertise of an entire IT department at a fraction of the cost of a full-time internal hire.
Will Pizzano, CISM is Founder of Sentant, a managed security and IT services provider that has helped dozens of companies achieve SOC 2 compliance. If you’re interested in help obtaining SOC 2 compliance, contact us.