Session Tokens
Modern cybersecurity threats have evolved beyond passwords and MFA, with attackers now targeting session tokens—the digital “all-access passes” stored in browsers after login. If hackers steal these tokens through malware, phishing, or malicious browser extensions, they can bypass MFA entirely and impersonate employees to access critical systems like Slack, AWS, or customer databases. For startups, this risk is especially dangerous because teams often use personal devices, maintain long session lifetimes, and grant broad admin privileges. To reduce exposure, companies should adopt identity-first security practices such as shorter session durations, device-bound authentication, hardware-backed passkeys, and continuous monitoring to detect suspicious activity before a breach escalates.

Beyond MFA: Why Your Session Tokens are the New Password
Today, the battleground of startup security has shifted beneath our feet. For one thing, modern threat actors aren't wasting time guessing passwords; instead, they’ve engineered sophisticated bypasses to ignore your MFA prompts entirely. Consequently, they are hunting the "Golden Ticket" of the distributed workforce: the session token.
The security landscape is no longer about the perimeter; rather, it’s about the persistence of access. Here is why your session tokens are the new password and why your startup must evolve its defensive posture before your next compliance audit or enterprise deal.
Key Takeaways
- The New Vulnerability: While MFA secures the initial handshake, sophisticated attackers now bypass it by harvesting session tokens directly from the endpoint browser. As a result, these tokens function as persistent digital keys, allowing an unauthorized party to impersonate a high-privilege user.
- Audit the Risk Profile: High-growth startups represent prime targets primarily because engineering leads often hold sweeping administrative rights while working from personal, unmanaged hardware.
- Harden Your Defenses: To mitigate this exposure, firms must drastically compress session lifetimes and enforce hardware-based validation. In doing so, they ensure tokens only execute on verified corporate assets.
- Leverage Strategic Maturity: Ultimately, transitioning from basic identity checks to a "Zero-Trust" framework is now a prerequisite for closing enterprise contracts.
Defining the Digital Handshake: What is a Session Token?
To defend architecture, a startup team has to get the how behind modern web. First of all, you need to understand that the Internet is "stateless". Specifically, that is, every time you click a link or refresh the page: at that moment, the server forgets who you are, or that 5 seconds ago you'd just logged in as a user.
Without a permanent identifier, you would need to type your password + MFA code every time you did any action.
The Mechanics of Persistent Access
This led developers to the "session" answer. Upon successful authentication, the server creates a unique random string called a session token. This token is then sent to your browser and stored there, i.e., as a cookie. The token is "given" by your browser to the server with every single request until you remain active within this window. Essentially, it's a free-flowing ID that says to the server, "This is still Sarah, and she already has permission to be here."
The Vulnerability of the "All-Access Pass"
However, this token is designed to be convenient and persistent, making it a target of opportunity. A token is a proof of something that you have (in contrast to a password, which you know as a secret). This means if an attacker copies that particular string of data from local storage for your browser, they do not have to know what the password is, nor intercept your phone. But instead, it just impersonates you by presenting stolen session tokens.
The Illusion of the "MFA Shield"
For years, the security industry viewed Multi-Factor Authentication as an impenetrable defense. This was based on the logic that physical access to a phone or biometric was a non-negotiable barrier for hackers. Nevertheless, several factors have changed this reality:
- The SaaS Workflow Gap: As startups pivoted to browser-based, SaaS-heavy environments, the traditional "set it and forget it" security mentality created a massive blind spot in session persistence.
- The Verification Loophole: For instance, when you authenticate into platforms like Slack or Jira, the system verifies your MFA once but then issues a digital identifier to avoid re-prompting you for every subsequent action.
- The Digital All-Access Pass: Consequently, these tokens, typically stored as cookies, serve as a continuous identity claim that allows users—or anyone who steals the token—to bypass MFA checks entirely for the remainder of the token's life.
The Rise of "Session Hijacking"
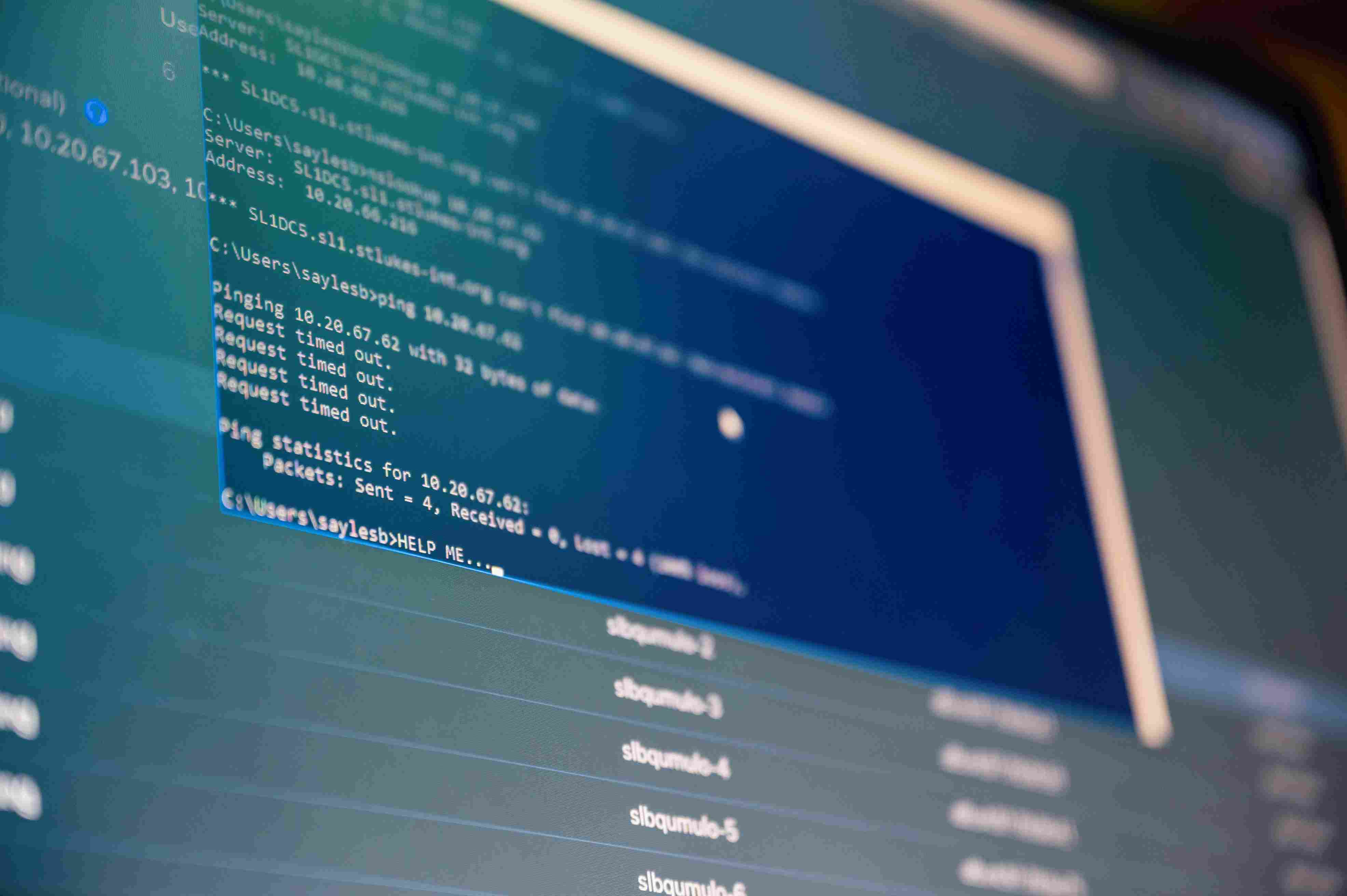
If a hacker can’t get your MFA code, they simply wait until after you’ve already provided it. Specifically, through sophisticated phishing or "infostealer" malware, attackers can now reach into an employee’s browser and copy those credentials. Next, they "inject" those tokens into their own browser. To the SaaS platform, the hacker’s browser looks identical to the employee’s browser. Thus, the hacker is instantly logged in—no password required, and no MFA prompt triggered.
For a startup, this is a nightmare scenario. Consider a case where an engineer has their personal laptop compromised by a malicious browser extension; suddenly, the attacker has the session token for the company’s production AWS environment.
Critical Vectors of Exploitation
- "Pass-the-Cookie" Attacks: This can be accomplished by infostealer malware on a local browser to steal active tokens from the cookie jar and use them for session replication at any remote machine without actually logging in.
- Adversary-in-the-Middle (AiTM) Phishing: In real-time, intercept the authentication flow by using proxy tools such as Evilginx, where the attacker gets the client challenge and both the password + token in conjunction to issue from the Auth service.
- Malicious Extensions: Via a malicious ("productivity") extension that injects scripts into the browser to operate in the background, scraping and exfiltrating tokens silently from every single tab.
- Side-Jacking on Unsecured Networks: Stealing unencrypted session identifiers over public Wi-Fi, compromising internal networks (side-jacking) by sniffing the active handshake before it reaches the destination server.
Why Startups are the Primary Targets
Imagine your startup just hit a major milestone. You’ve implemented MFA across every single app—Slack, GitHub, AWS, and your CRM. Furthermore, you’ve told your investors that your perimeter is secure. But while you’re patting yourself on the back for closing the front door, the back window is wide open.
In fact, bad actors love startups for three specific reasons:
- High-Privilege Friction: In a 20-person startup, almost everyone has "Admin" or "Owner" access to something critical; hence, stealing one token from a founding engineer is often a "Game Over" event.
- The BYOD Culture: Startups often allow employees to work from personal laptops that lack enterprise-grade protection. As a result, these devices are more vulnerable to infostealers grabbing browser cookies.
- Long Session Lifetimes: To avoid "annoying" their team, many founders set their session timeouts to 30 days or even "Indefinite." Unfortunately, this means a stolen token is a gift that keeps on giving.
The Anatomy of a Token Theft
Let’s look at how this actually happens in a modern startup environment. Take, for example, "Sarah," a marketing lead at a Series A fintech startup. Sarah is diligent; she uses a password manager and has MFA enabled on everything. However, one afternoon, she receives a convincing email about a new industry report. She clicks a link that leads to a slightly suspicious site, which silently downloads a tiny piece of malware—an "infostealer."
This malware doesn't look for her passwords. Instead, it heads straight for the Cookies folder in her Chrome profile. Following this, it zips up the session tokens for her Gmail, Slack, and HubSpot instance. Ten minutes later, an attacker in another country has imported those cookies.
When they open Slack, they don't need Sarah's password or her phone for a push notification. They are simply in. From there, they can read private channels, download sensitive customer data, or find API keys pinned in a "Dev" channel.
Beyond MFA: How to Protect Your Startup
If MFA is no longer enough, what is? Moving "Beyond MFA" doesn't mean getting rid of it; rather, it means layering defenses that acknowledge the reality of session theft. At Sentant, we advise our clients to move toward an Identity-First security posture:
- Shorten Session Durations: Terminate "Forever Tokens" immediately. By shrinking the "Window of Opportunity," a stolen cookie becomes useless in 8 hours instead of 8 days.
- Implement Device Binding: Require that a session token only functions if used on a managed, encrypted device verified by your Identity Provider (Okta, Google, or JumpCloud).
- Deploy Hardware-Bound Passkeys: Utilize WebAuthn protocols to bind authentication to specific hardware, thereby making it nearly impossible for a phishing site to intercept the handshake.
- Monitor for Impossible Travel: Audit your logs for alerts where, for instance, a token is used in San Francisco at 9:00 AM and then appears in Eastern Europe at 9:05 AM.
- Adopt Continuous Access Evaluation: Implement real-time monitoring that can revoke active tokens the moment a device's risk profile changes.
The Cultural Shift: A Competitive Advantage
For many founders, this sounds like "more friction." Nevertheless, in 2026, security is no longer just a checkbox for your SOC2 audit; it’s a requirement for enterprise sales. When you sit down with a Fortune 500 customer, their CISO is going to ask: "How do you protect your active sessions?"
Being able to answer those questions confidently doesn't just protect your data; moreover, it accelerates your deal cycles. It shows that you aren't just a "scrappy startup," but instead, a mature organization that understands the modern threat landscape.
How Sentant Helps
At Sentant, we specialize in helping high-growth startups build these "Next-Gen" security foundations without slowing down their engineering teams. Rather than just giving you a list of problems, we help you implement the tools—from MDM to Zero-Trust networking—that make session hijacking a non-issue.
The "Password" era is over. The "MFA-Only" era is ending. Now, it’s time to secure your sessions, protect your session tokens, and build a startup that is truly resilient.
Frequently Asked Questions
Q: If I have MFA enabled, can my accounts still be hacked?
A: Yes. However, MFA does not protect against "Session Hijacking". MFA. When you log in to a service, they give your browser a session token. Now, an attacker who has stolen that token can use it anywhere on the Internet and is able to gain access without any MFA device ever being present.
Q: How do hackers actually steal tokens from my employees?
A: The most common method is through "Infostealer" malware. Typically, this is hidden in suspicious browser extensions. Once installed, it silently copies the Cookies folder and sends those active tokens to the attacker’s server.
Q: Can I simply enable a VPN to prevent token stealing?
A: Not effectively. While a VPN encrypts your data during transit on the internet, it does not secure what is in files that are left at rest on your computer. No matter the VPN, if malware is on a laptop, an attacker can take over local browser token storage.
Q: Why is "Session Hijacking" suddenly such a big deal?
A: As more companies move toward passwordless logins, attackers have realized it is much harder to break a login than it is to steal a token after the login is complete. In fact, research shows that over 85% of successful breaches now involve session hijacking.
Q: What is the most effective way to protect a startup from token theft?
A: The gold standard is Device Binding. This means that a session token can be cryptographically "locked" to a specific, governed company laptop. So if an attacker, for instance, on their own machine, used a stolen token, the service would detect that mismatch and automatically kill the session.
Will Pizzano, CISM is Founder of Sentant, a managed security and IT services provider that has helped dozens of companies achieve SOC 2 compliance. If you’re interested in help obtaining SOC 2 compliance, contact us.