Remote IT Support for VC Firms
Remote IT support for VC firms ensures secure, fast, and reliable access to critical systems and sensitive investment data while enabling teams to work efficiently from anywhere. It provides enterprise-level cybersecurity, cloud management, and compliance support without the cost of building a full in-house IT team. This helps firms reduce downtime, prevent data breaches, and maintain a competitive edge in high-speed deal environments.

Mastering Remote IT Support for VC Firms: A San Francisco Tactical Guide
The venture capital landscape in San Francisco doesn’t tolerate digital friction. For firms managing high-stakes portfolios and massive capital infusions, a flickering server or a breached data room isn't just an "IT issue"—it’s a deal-breaker. Implementing remote IT support for VC firms has shifted from a luxury to a baseline requirement for maintaining operational velocity and safeguarding the proprietary startup data that fuels the Bay Area economy.
Key Takeaways
- Zero-Trust Security: VC firms handle high-value financial intelligence, necessitating enterprise-grade encryption and persistent threat hunting.
- Operational Agility: Remote infrastructure allows for instantaneous troubleshooting, bypassing the logistical nightmare of San Francisco traffic.
- Cost-Efficient Scaling: Outsourcing provides access to a full stack of senior engineers without the overhead of a full-time, in-house technical department.
- Regulatory Compliance: Managed services ensure your data storage meets the rigorous standards required for modern financial auditing and SEC oversight.
Why Is Remote IT Support for VC Firms Essential in the Modern Market?
Remote IT support for VC firms provides the specialized technical oversight required to manage distributed networks, secure sensitive investment data, and maintain 24/7 uptime. By leveraging off-site engineering teams, firms can access high-level cybersecurity expertise and cloud management tools that would be prohibitively expensive to build internally. This model ensures that regardless of where your partners are—whether in a SOMA boardroom or at a tech conference in London—their connection remains secure and their hardware stays operational.
The Strategic Framework for VC Tech Resilience
- Infrastructure Hardening: We begin by auditing your current network "perimeter."
- Deploy Multi-Factor Authentication (MFA) across all SaaS platforms and local endpoints.
- Implement hardware-level encryption for all partner devices to protect against physical theft.
- Cloud Migration & Management: Moving the firm’s workflow to a secure, redundant cloud environment.
- Architect private cloud storage solutions that integrate seamlessly with your existing deal-flow software.
- Establish automated, geographically dispersed backups to ensure disaster recovery in seconds, not days.
- Active Threat Mitigation: Transitioning from reactive "break-fix" habits to proactive hunting.
- Utilize AI-driven endpoint detection to identify suspicious behavior before a breach occurs.
- Conduct regular phishing simulations to train partners on spotting sophisticated social engineering.
Critical Industry Entities & Definitions
- Endpoint Detection & Response (EDR): A technology that constantly monitors end-user devices to detect and respond to cyber threats like ransomware.
- SOC (Security Operations Center): A centralized unit that deals with security issues on an organizational and technical level.
- Data Room Security: The specialized encryption and access protocols used to protect sensitive documents during the due diligence process.
- Business Continuity Planning (BCP): A technical roadmap that defines how a VC firm will continue operating during an unplanned service disruption.
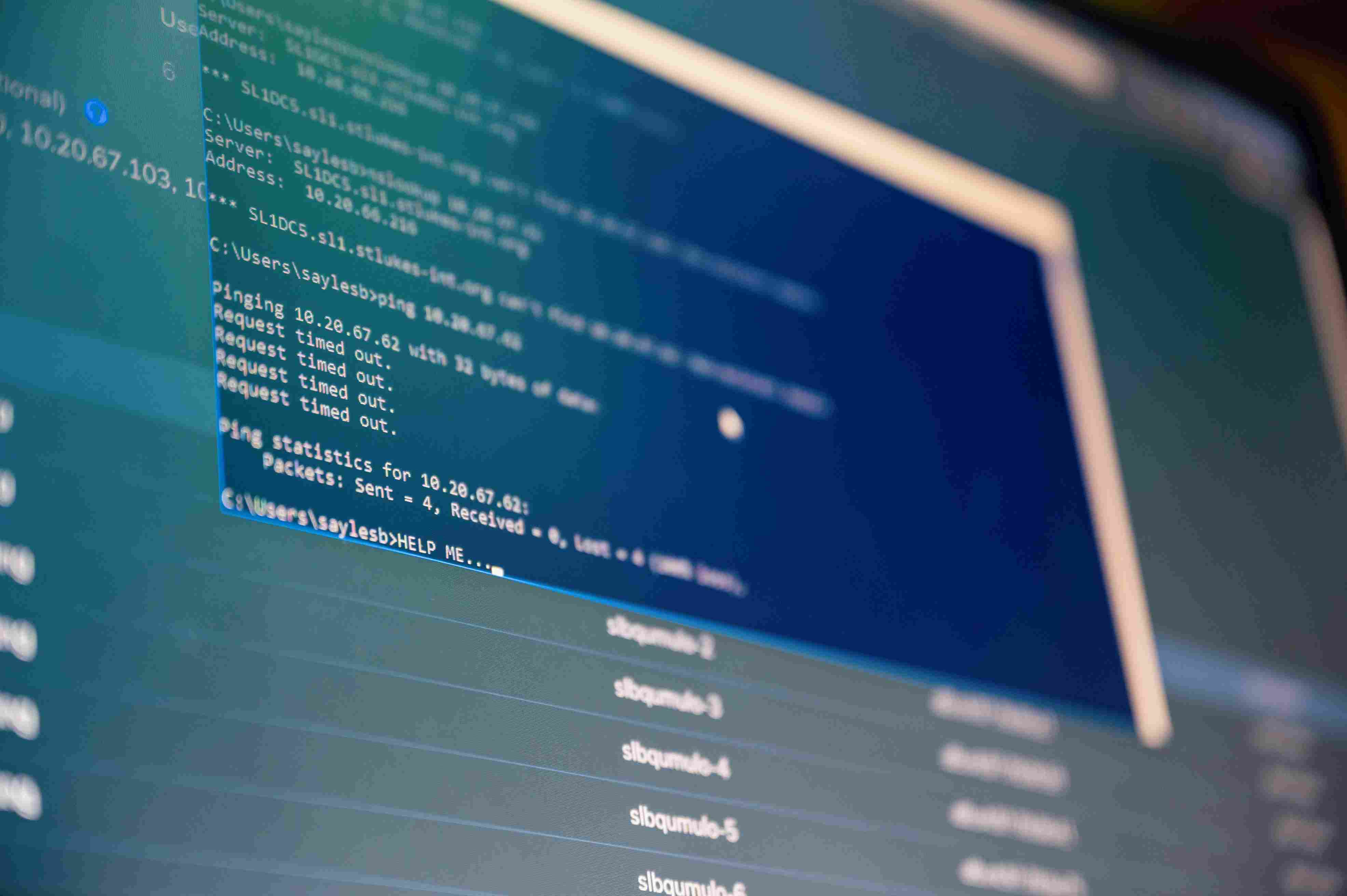
Expert Perspective: The "Shadow IT" Trap
Pro Tip: The biggest risk we see in San Francisco VC firms isn't a hacker—it's "Shadow IT." This happens when partners use personal Dropbox or Slack accounts for deal flow because the official systems are too clunky. Remote IT support for VC firms must focus on making secure tools faster and more intuitive than the personal ones. If the secure path is the path of least resistance, your partners will stay on it.
Mastering the Future of VC Technology
Venture capital is a game of speed and information. If your technology isn't actively helping you win that game, it's a liability. By integrating specialized technical oversight into your daily workflow, you eliminate the "hidden tax" of downtime and the catastrophic risk of a data leak. In the hyper-competitive San Francisco market, the most successful firms are those that treat their IT infrastructure as a competitive advantage rather than an afterthought.
Secure your firm's future with the experts at Sentant. Call (415) 555-0199 today for a high-level audit and see how our remote IT support for VC firms can streamline your operations.
Frequently Asked Questions
How does remote IT support handle physical hardware failures?
When a partner’s laptop fails, we manage the logistics of a secure hardware swap. In the interim, we provide secure virtual environments so the user can keep working on any device without compromising firm data.
Is it safe to give an outside firm access to our VC data?
Yes, provided you choose a firm like Sentant that utilizes rigorous compliance standards and encrypted access. We don't "see" your data; we manage the "pipes" it travels through to ensure it remains private.
How fast is the typical response for an urgent deal-breaker issue?
For critical issues affecting a live deal or partnership meeting, our remote engineers are typically logged in and troubleshooting within minutes, regardless of the time of day.
Does remote support help with SEC and financial audits?
Absolutely. We maintain detailed logs of security events, patch history, and access records, which are essential for proving technical compliance during a regulatory audit.
Can we keep our current software and just move the support?
Yes. We specialize in managing existing VC tech stacks, optimizing them for security, and gradually recommending upgrades only when they provide a clear ROI for your specific workflow.
Will Pizzano, CISM is Founder of Sentant, a managed security and IT services provider that has helped dozens of companies achieve SOC 2 compliance. If you’re interested in help obtaining SOC 2 compliance, contact us.