Austin TX Cybersecurity Company
A local Austin, TX cybersecurity company provides proactive, multi-layered protection—like 24/7 monitoring, threat hunting, and compliance support—to defend businesses from rapidly evolving cyber threats. Their on-site presence, fast incident response, and understanding of local regulations make them far more effective than generic providers. By partnering with a specialized local firm, businesses can reduce risk, maintain uptime, and build a secure foundation that scales with growth.

Why Your Local Austin TX Cybersecurity Company is the Only Thing Between You and a Total Breach
In the Silicon Hills, the threat landscape shifts faster than the traffic on I-35. Relying on a generic, "coast-to-coast" security provider is a gamble most Central Texas firms can't afford to lose. When you hire a dedicated Austin TX cybersecurity company, you aren't just buying software; you’re recruiting a localized defense force that understands the specific regulatory and technical pressures of the Texas business ecosystem.
Key Takeaways
- Proactive Defenses: Modern security isn't about reacting to a virus; it's about hardening the perimeter before the first packet is sent.
- Rapid On-Site Support: Local presence means boots-on-the-ground help when a physical hardware breach or network failure occurs.
- Compliance Expertise: Navigating Texas-specific data privacy mandates requires a partner who knows the local legal landscape.
- Scalable Infrastructure: Your security stack should grow at the same rate as your Austin-based startup or enterprise.
What Does an Austin TX Cybersecurity Company Actually Do for Your Business?
An Austin TX cybersecurity company acts as a digital sentry, employing advanced threat hunting, 24/7 network monitoring, and encryption protocols to shield your assets. Beyond just installing a firewall, these specialists architect a multi-layered defense system tailored to your specific hardware, remote workforce habits, and cloud dependencies. They ensure that your proprietary data remains inaccessible to unauthorized actors while maintaining high system uptime.
What Are the Non-Negotiable Traits of a Reliable Security Provider?
You need a partner with deep-tier technical experience, a verifiable track record in incident response, and a stack of modern tools like EDR and SOC-as-a-Service. The reality is that "knowing IT" isn't the same as "knowing security." A true master of the craft looks for the vulnerabilities in your "shadow IT"—those unmanaged apps your employees use—and closes the gaps that generic automation tools usually miss.
- Battle-Tested Experience: Look for engineers who have managed breaches in the real world, not just in a simulator.
- Zero-Trust Architecture: Every user and device must be verified, whether they are in the office or working from a coffee shop on South Congress.
- Transparent Reporting: You shouldn't need a computer science degree to understand your monthly risk assessment.
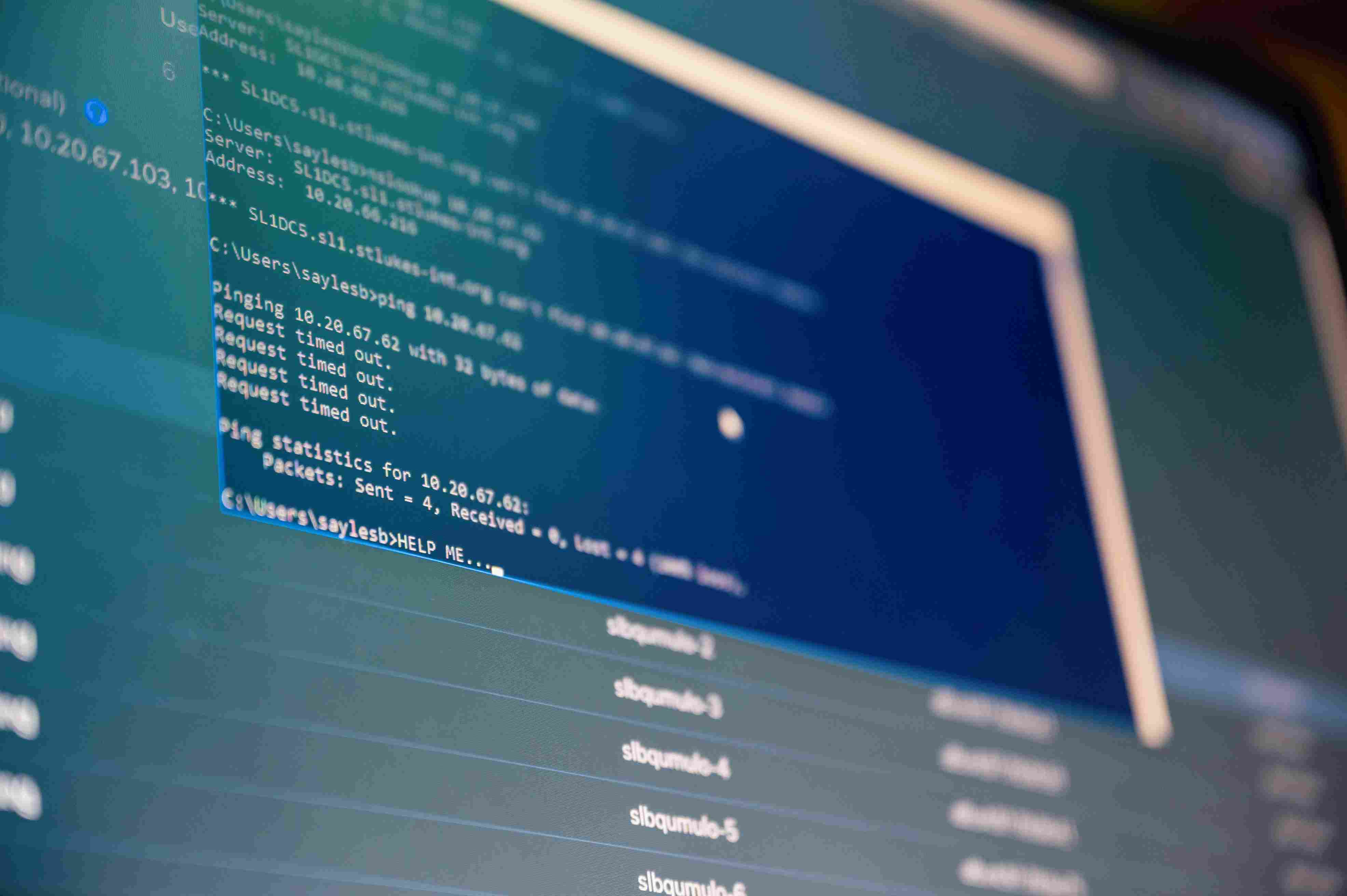
How Fast Should an Incident Response Team React to a Live Threat?
The "Golden Hour" of a cyberattack is the first sixty minutes; a top-tier provider should offer 24/7/365 monitoring with immediate triage capabilities. If a ransomware strain hits your server at 3 a.m. on a Sunday, you can't wait until Monday morning for a ticket response. Slow reaction times exponentially increase the cost of data recovery and the likelihood of permanent brand damage.
Why Should You Demand Compliance and Risk Management Audits?
Regulatory standards like HIPAA, SOC2, or Texas-specific privacy laws require constant vigilance and documented proof of security controls. A professional Austin TX cybersecurity company doesn't just "set it and forget it." They perform regular penetration testing and vulnerability scans to ensure you stay on the right side of the law. This isn't just about avoiding fines; it's about proving to your clients that their data is handled with professional-grade care.
The Strategic Framework: The 4 Phases of Digital Hardening
- The Perimeter Audit
- Map every entry point, from VPNs to physical office Wi-Fi.
- Identify "End-of-Life" hardware that no longer receives critical security patches.
- Active Threat Hunting
- Deploy AI-driven monitors that flag "impossible travel" logins (e.g., a login from Austin followed by one from overseas 10 minutes later).
- Isolate suspicious files in a "sandbox" environment before they touch your main server.
- Employee Resilience Training
- Run simulated phishing campaigns to see who clicks the "bad" links.
- Conduct workshops on password hygiene and Multi-Factor Authentication (MFA).
- Disaster Recovery Orchestration
- Establish off-site, immutable backups that hackers can’t encrypt.
- Create a "Playbook" for exactly who does what if the network goes dark.
Technical Execution & Use-Cases
- Risk Mitigation: Implementing "Least Privilege" access, ensuring employees only see the data they absolutely need for their job.
- Growth Strategy: Building a secure cloud environment in AWS or Azure that allows you to hire talent anywhere without leaking IP.
- Cloud Hardening: Securing the "SaaS sprawl" by unifying logins under a single, encrypted identity provider.
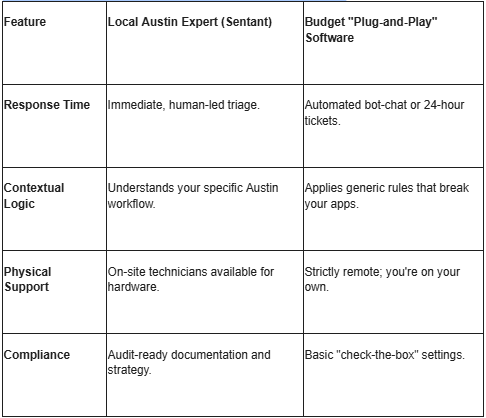
Comparison: Local Experts vs. Budget Automation
Expert Perspective: The "Hidden" Vulnerability
Most business owners obsess over hackers, but the biggest threat is often configuration drift. You set up a secure server three years ago, but over time, employees change settings, add insecure plugins, and open "backdoors" for convenience. A true Austin TX cybersecurity company performs "continuous posture management" to snap those settings back to a secure baseline. If you aren't auditing your configurations quarterly, you're leaving the door unlocked.
Mastering the Future of Austin Tech Security
The digital landscape in Austin is getting noisier, and the attackers are getting smarter. You can't fight a modern war with a medieval shield. By shifting your mindset from "IT maintenance" to "Active Defense," you protect not just your files, but your company's reputation and its future. Sentant provides the high-level expertise needed to navigate this chaos, ensuring your team can focus on innovation while we handle the incoming fire.
Take the first step toward a hardened perimeter. Explore our deep-dive guides on cloud security or reach out to our Austin team for a comprehensive risk assessment.
Frequently Asked Questions
What does an Austin, TX cybersecurity company do?
They provide a specialized layer of protection for your business, including 24/7 monitoring, threat mitigation, and strategic planning to prevent data breaches and downtime.
Why is cybersecurity important for Austin businesses specifically?
Austin is a high-value target for hackers due to its dense concentration of tech, healthcare, and finance startups that handle massive amounts of sensitive proprietary data.
How much do these security services cost?
Pricing is modular; it depends on the number of users you have, the complexity of your cloud environment, and whether you require 24/7 SOC monitoring or just basic protection.
Can a small business benefit from a cybersecurity firm?
Absolutely. In fact, small businesses are often targeted more frequently because hackers assume their defenses are weak. Scalable plans allow small firms to get enterprise-grade protection.
How do I choose the right provider in Central Texas?
Focus on their incident response time, their familiarity with your specific industry's regulations, and their ability to provide local, on-site support when things get critical.
Will Pizzano, CISM is Founder of Sentant, a managed security and IT services provider that has helped dozens of companies achieve SOC 2 compliance. If you’re interested in help obtaining SOC 2 compliance, contact us.

.jpeg)