What to Know About IT Services for Venture Capital Firms
IT services for venture capital firms focus on building secure, scalable, and always-on infrastructure to protect sensitive data and keep deal flow moving without disruption. By adopting zero-trust security, compliance-ready cloud systems, and robust disaster recovery, firms reduce risk while enabling fast, seamless collaboration. A proactive, managed IT approach ensures operational resilience, minimizes downtime, and turns technology into a competitive advantage rather than a liability.

What to Know About IT Services for Venture Capital Firms: A Guide to Secure Operations
Venture capital firms in the high-stakes San Francisco, CA, landscape don't just rely on capital; they rely on bulletproof infrastructure. If your technology lags during a term sheet negotiation or a due diligence sprint, you aren't just losing time—you’re losing the deal. Understanding what to know about IT Services for venture capital firms is about shifting from reactive "break-fix" mentalities to a proactive, hardened stance that protects your portfolio and your reputation.
Key Takeaways
- Zero-Trust Architecture: Modern VC IT must assume the network is compromised, requiring strict identity verification.
- Compliance-First Cloud: Systems must be pre-configured to meet rigorous financial regulatory standards.
- Operational Resilience: Redundant backup protocols ensure that a localized San Francisco power grid failure won't halt your deal flow.
- Scalable Perimeter Security: Your tech stack must expand instantly as you onboard new partners or regional offices.
Why Is Cyber Defense Essential for VC Infrastructure?
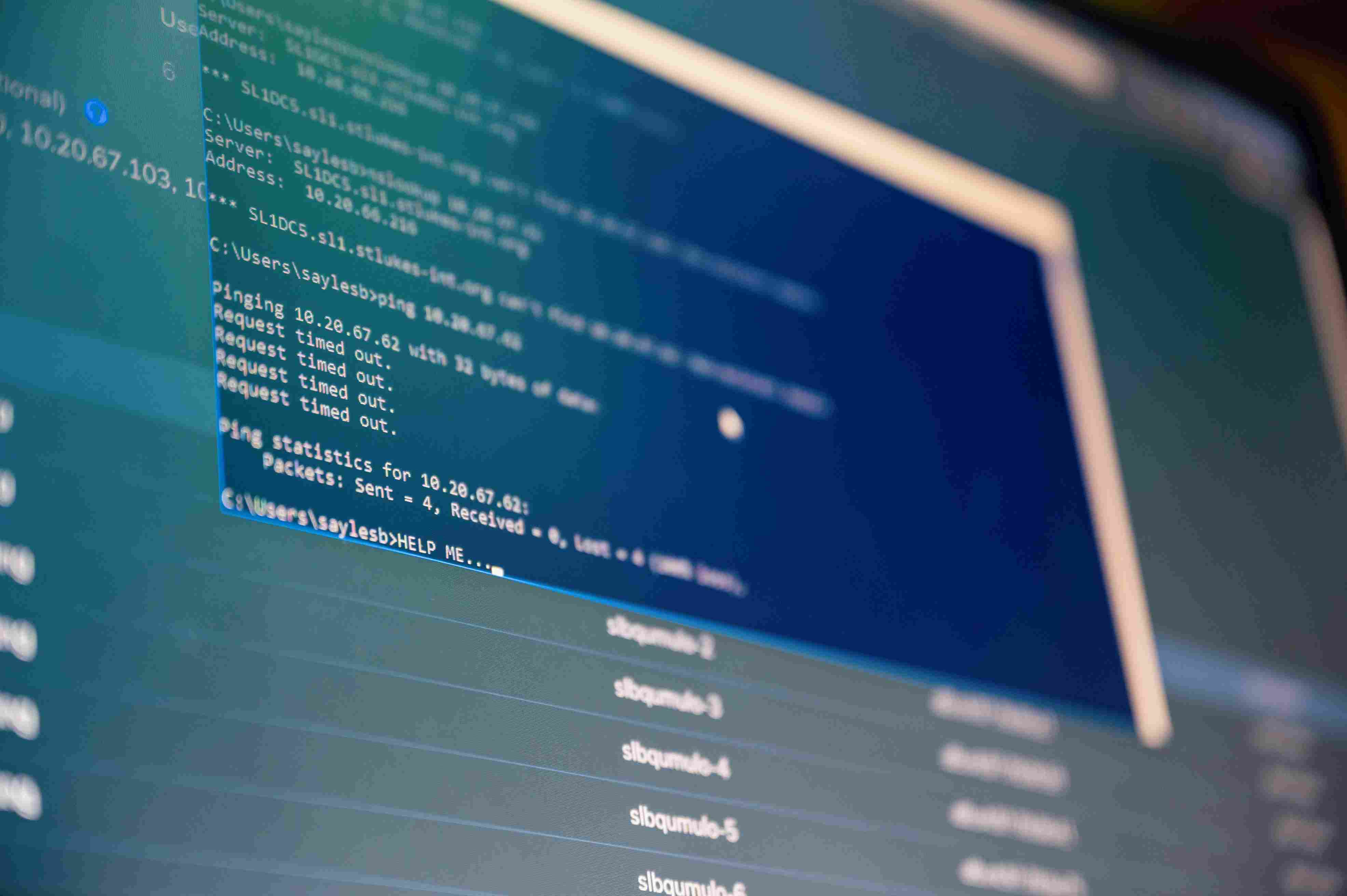
The high-value nature of investor data and proprietary deal flow makes venture firms a "whale" target for sophisticated phishing and ransomware. To mitigate this, firms must deploy multi-layered encryption and continuous endpoint monitoring. If you aren't treating your data with the same security rigor as a Tier-1 bank, you are operating with a massive blind spot that sophisticated LPs will eventually sniff out.
Risk Mitigation & Growth
- Identity Access Management (IAM): Provisioning permissions based strictly on the "least privilege" principle to stop internal leaks.
- Encrypted Communication Channels: Moving sensitive deal talk off of unencrypted SMS and into hardened, audited platforms.
- Automated Threat Hunting: Using AI-driven tools that flag an anomalous login from an unrecognized IP in seconds.
How Does Cloud Infrastructure Power Modern Deal Flow?
Cloud systems allow San Francisco, CA investment teams to move at the speed of a handshake by providing secure, instant access to data rooms. We are long past the days of clunky on-premise servers; today’s Master Craftsman approach involves a "cloud-native" posture where every file is synchronized, version-controlled, and accessible from a partner's iPad at a coffee shop or a boardroom.
Technical Execution Framework
- Environment Isolation: Segmenting your internal firm data from external-facing portfolio company portals.
- Implement VLANs (Virtual Local Area Networks) to ensure data doesn't "bleed" across departments.
- Enforce hardware-based 2FA (like YubiKeys) for all administrative cloud access points.
- Data Residency Controls: Ensuring your stored information complies with specific jurisdictional requirements.
- Set geo-fencing rules to prevent data from being accessed or stored in high-risk regions.
- Maintain real-time audit logs for every document view or download.
- Seamless Integration: Connecting your CRM, accounting software, and file storage into a unified ecosystem.
- Utilize API-driven workflows to automate repetitive data entry between deal-tracking tools.
What Role Does Disaster Recovery Play in Business Continuity?
A single hour of downtime during a funding round is a catastrophic failure that most firms can't afford. You need a "Warm Standby" recovery model—meaning your data is backed up every few minutes to a secondary, off-site location. When the "big one" hits or a simple server glitch occurs, the Master Craftsman doesn't panic; they simply flip the switch to the redundant system and keep the wires moving.
How Can Managed Help Desks Prevent Technical Friction?
The reality on the ground is that partners don't have time to troubleshoot a VPN glitch when they are ten minutes away from a pitch. A specialized help desk understands the specific software VCs use—from specialized cap table management tools to high-end video conferencing. It’s about having a "boots on the ground" partner in San Francisco, CA, who knows that in this industry, technical friction is the enemy of ROI.
Essential Entity Grounding
- SOC 2 Type II: A rigorous auditing procedure that ensures your service providers manage your data securely.
- End-to-End Encryption (E2EE): A system of communication where only the communicating users can read the messages.
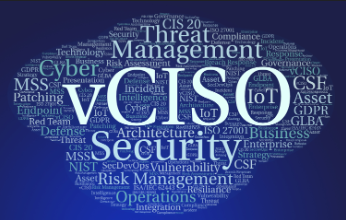
- Virtual CISO (vCISO): Providing high-level security leadership without the $300k/year overhead of a full-time hire.
- SIEM (Security Information and Event Management): Software that provides real-time analysis of security alerts generated by applications.
Why Is Regulatory Compliance a Technical Requirement?
What to know about IT Services for venture capital firms is that compliance isn't just a legal checkbox; it's a technical configuration. Whether it’s SEC requirements or regional privacy laws, your IT provider must bake these rules into your file-sharing and email retention policies. If your IT guy doesn't know what an "Immutable Audit Trail" is, he's putting your firm at risk of a major fine.
Expert Perspective: The "Shadow IT" Trap
Pro Tip: The biggest threat to your firm isn't a hacker; it's a partner using a personal Dropbox account because the firm's system is too slow. To stop "Shadow IT," you must make the secure way the easiest way. If your security protocols add ten minutes of friction to a task, people will bypass them. Build a workflow that is as fast as it is fortified.
Mastering the Future of Venture IT
Winning in the venture space requires a tech stack that is as aggressive and agile as your investment strategy. By integrating elite cybersecurity, seamless cloud mobility, and 24/7 technical support, your firm eliminates the digital hurdles that slow down capital deployment. The goal is simple: make your technology invisible so your talent can focus on the next unicorn.
Sentant specializes in the "Master Craftsman" approach to technology—building high-performance, secure environments for the most demanding firms in the Bay Area. We don't just fix computers; we engineer the competitive advantage you need to dominate the San Francisco, CA market.
Click here to secure your firm's infrastructure with Sentant and see what to know about IT Services for venture capital firms in action.
Frequently Asked Questions
What are the primary IT requirements for a new VC firm?
A new firm requires a secure cloud identity (like Google Workspace or Microsoft 365 hardened with advanced security), an encrypted file-sharing system for data rooms, and a robust mobile device management (MDM) policy to protect partner phones and laptops.
How does Sentant protect against social engineering attacks?
We implement advanced email filtering to catch "spoofed" executive names and provide ongoing security awareness training. We also enforce hardware-based MFA, which is virtually impossible for a remote hacker to bypass, even if they have a partner's password.
Is cloud storage safe for highly confidential term sheets?
Yes, provided it is configured correctly with AES-256 encryption and strict access controls. Most "leaks" happen due to human error—like a folder accidentally being set to "public"—which is why professional managed services are critical for oversight.
What is the benefit of a Virtual CISO for an investment firm?
A vCISO provides the strategic roadmap for security and compliance without the cost of a C-suite salary. They ensure your firm can pass LP due diligence questionnaires with flying colors, which is essential for successful fundraising.
How often should a venture capital firm perform a security audit?
At a minimum, a full technical audit should be performed annually. However, continuous monitoring is the modern standard, as it identifies vulnerabilities in real-time rather than waiting for a yearly check-up to find a breach.
Will Pizzano, CISM is Founder of Sentant, a managed security and IT services provider that has helped dozens of companies achieve SOC 2 compliance. If you’re interested in help obtaining SOC 2 compliance, contact us.