Best Cybersecurity Practices for Startups
Startups in 2026 face growing cyber threats, making strong security practices essential for protecting sensitive data, maintaining customer trust, and supporting business growth. Key cybersecurity strategies include using multi-factor authentication, Zero Trust security, endpoint detection tools, automated backups, employee security training, and continuous monitoring to reduce risks from phishing, ransomware, and human error. Sentant helps startups build scalable, security-first environments with managed protection, compliance support, and proactive threat monitoring designed for fast-growing companies.

Best Cybersecurity Practices for Startups: A Battle-Hardened Guide for 2026
In the high-stakes environment of San Francisco, CA, your startup is a target long before you hit your first $1M in ARR. Cyber threats aren't just a technical glitch; they are an existential risk that can burn through investor trust and customer confidence overnight. Implementing the best cybersecurity practices for startups means moving beyond "set it and forget it" firewalls. You need a gritty, defensive posture that treats security as a core business function, not a weekend project.
Sentant specializes in architecting secure digital foundations that scale with the frantic pace of the Bay Area tech scene. We don't do "academic" security—we provide the "boots on the ground" expertise required to shield your intellectual property from AI-driven phishing and sophisticated ransomware.
Key Takeaways
- Identity is the New Perimeter: Traditional office walls are dead; securing user identities with hardware-backed MFA is the only way to stop 2026-era credential harvesting.
- The AI Arms Race: Attackers are using autonomous AI agents to probe your network 24/7. Your defense must be just as automated and twice as fast.
- Compliance is a Growth Lever: Getting "SOC 2 Ready" early isn't just about paperwork—it’s the key to unlocking enterprise-level contracts and closing Series A rounds.
- Zero Trust isn't a Buzzword: Assuming every connection is hostile—even from inside your own Slack—prevents lateral movement during a breach.
- Immutable Recovery: In the age of multi-stage extortion, an off-site, unchangeable backup is the only thing standing between you and a $5M ransom demand.
What Are the Best Cybersecurity Practices for Startups to Implement Now?
The best cybersecurity practices for startups involve a layered strategy focusing on Identity and Access Management (IAM), automated patch cycles, and rigorous endpoint detection. By deploying Managed Detection and Response (MDR) tools and enforcing the "Principle of Least Privilege," startups can mitigate the vast majority of threats. The reality is that 95% of cloud breaches in 2026 stem from misconfigurations and human error, not genius-level hacking.
The Strategic Framework for Startup Defense
- Hardening the Human Layer
- Conduct "Live Fire" phishing simulations that mirror the latest AI-generated deepfake email tactics.
- Establish a "No-Blame" culture where employees feel comfortable flagging a suspicious San Francisco, CA district court subpoena before clicking.
- Locking Down the Infrastructure
- Audit AWS/GCP buckets weekly to ensure no PII (Personally Identifiable Information) is sitting in a public-facing repository.
- Replace legacy VPNs with Zero Trust Network Access (ZTNA) to limit the "blast radius" if a laptop is stolen at a South of Market coffee shop.
- Automating Technical Hygiene
- Deploy Mobile Device Management (MDM) to enforce full-disk encryption and remote wipe capabilities across your distributed team.
- Use automated vulnerability scanners to identify and patch high-risk flaws before the CVE (Common Vulnerabilities and Exposures) is even published.
- Codifying Incident Response
- Build a "Break Glass" protocol that clearly defines who has the authority to pull the plug on production during a suspected breach.
- Maintain air-gapped, encrypted backups that allow for a full system restoration in hours, not weeks.
Why Does Cybersecurity Matter for Startups in the Bay Area?
Cybersecurity is the bedrock of due diligence, and a single breach can incinerate a startup's reputation before it’s even reached product-market fit. Hackers view San Francisco, CA startups as "soft targets" that hold valuable intellectual property but lack the million-dollar security teams of a Google or Meta. Strong protection builds the "Trust Equity" needed to survive deep-dive audits from VC firms and enterprise-scale clients.
How Do You Implement Core Security Practices for Strong Protection?
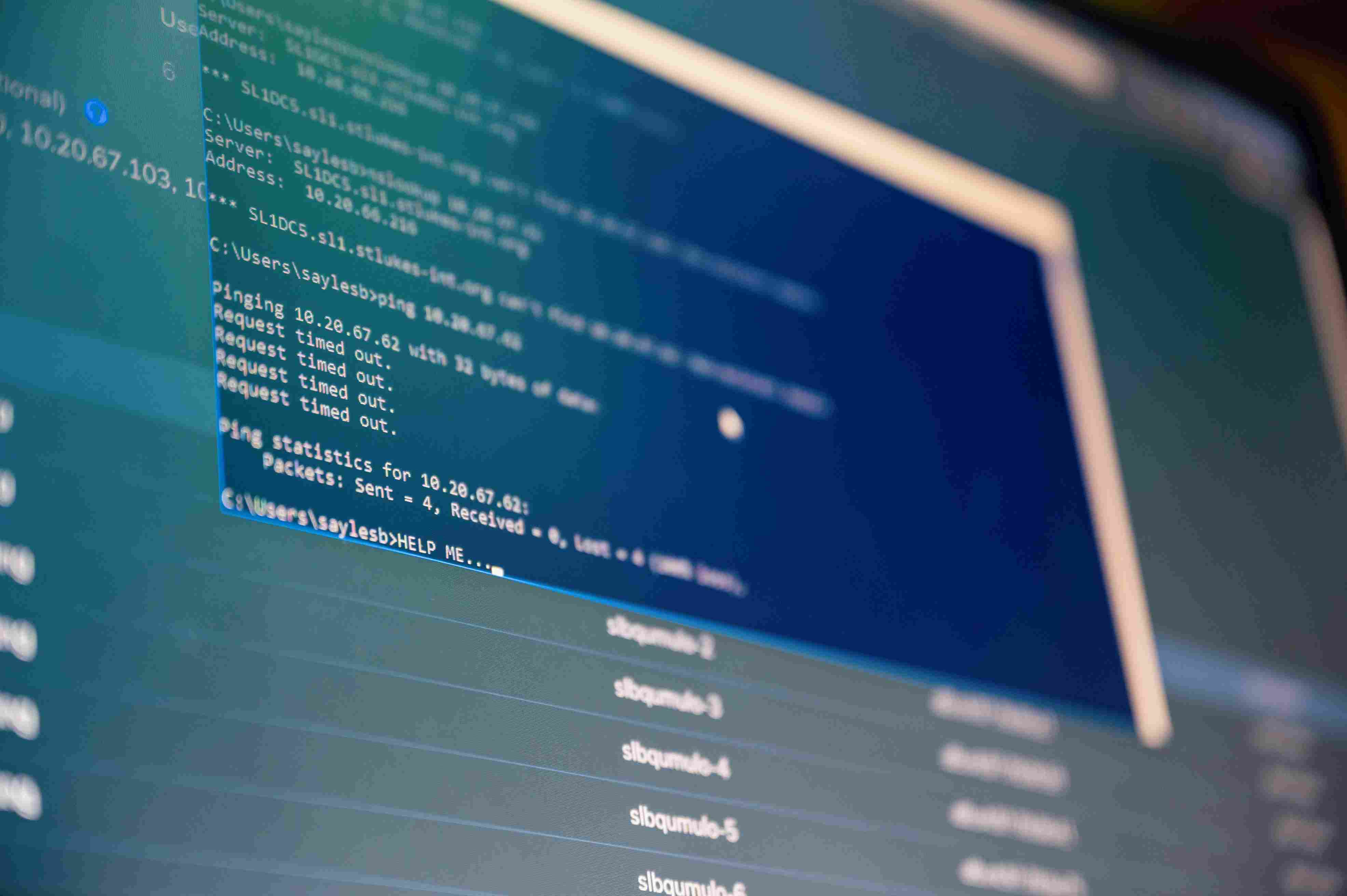
Strong protection starts with visibility—you can't defend a server you forgot you spun up for a 2024 demo. In the current landscape, the best cybersecurity practices for startups demand that you inventory every SaaS tool and API key in your stack. The "boots on the ground" reality is that most breaches are "dumb"—a developer leaves a root password in a public GitHub repo or fails to update a legacy database.
- Endpoint Detection (EDR): Install advanced sensors on every workstation to spot "fileless" malware that standard antivirus misses.
- Shadow IT Audits: Use network traffic analysis to find employees using unapproved, insecure AI tools that might be leaking your source code.
- Zero-Trust Wi-Fi: Treat every network like a public Starbucks connection; use encrypted tunnels for every internal communication.
What Is the Role of Identity and Access Management?
Identity and Access Management (IAM) ensures that only the right people have the minimum amount of access needed to do their specific jobs. If your marketing intern has root access to your production database, you’re one phish away from a total wipeout. Identity is the new perimeter in 2026, especially for remote-first startups where traditional firewalls offer zero protection.
- Single Sign-On (SSO): Centralize your access through Okta or Google Workspace so you can kill every account with one click when someone leaves.
- FIDO2/WebAuthn: Move beyond SMS codes; use hardware keys or biometrics to stop SIM-swapping and "man-in-the-middle" attacks.
- Quarterly Access Reviews: Ruthlessly prune permissions; if a dev hasn't logged into the billing portal in 90 days, pull their access.
How Can Startups Improve Network Security and Protection?
Modern network security for startups focuses on securing the data flow between distributed nodes, rather than guarding a physical office. In the San Francisco, CA startup scene, your "network" is a mesh of home Wi-Fi and co-working spaces. You need to enforce encryption at the application layer and use smart DNS filtering to block malicious domains before the browser even loads them.
- ZTNA Adoption: Replace clunky, vulnerable VPNs with Zero Trust tunnels that only grant access to specific apps, not the whole network.
- DNS Filtering: Use tools like Cloudflare or Cisco Umbrella to prevent employees from landing on malware-hosting "typo-squatting" sites.
- WAF/API Protection: Since APIs are the backbone of modern apps, use a Web Application Firewall to block bot-driven "credential stuffing" attacks.
Why Are Data Protection and Backup Systems Critical?
Data protection and backup systems serve as your final line of defense against the "double extortion" tactics of modern ransomware. In the world of the best cybersecurity practices for startups, a backup is only real if it’s "air-gapped"—meaning a hacker who gets into your main cloud account can't delete your secondary copies. Encryption isn't just for compliance; it's what keeps your data useless to a thief.
- Immutable Backups: Use S3 Object Lock or similar tools to ensure that once data is written, it cannot be deleted or encrypted by a third party for a set period.
- AES-256 at Rest: Ensure every database and cloud bucket is encrypted by default; never leave the "unencrypted" box checked.
- The Fire Drill: Perform a live restoration test every quarter. If you haven't tried to rebuild your environment from scratch, you don't actually have a backup plan.
Expert Perspective: The "Supply Chain" Trap
Most startups get hacked through their vendors, not their own code. If you're using a third-party library or an obscure SaaS tool for payroll, you've just inherited their security problems. Here’s the pro tip: Always ask for a SOC 2 Type II report or a CAIQ (Consensus Assessments Initiative Questionnaire) from your vendors. If they can't provide one, they aren't ready for your data.
How Does Employee Awareness and Training Reduce Risk?
Employee training turns your team into a distributed "human firewall" that can spot the subtle red flags of a social engineering attack. Tech-heavy startups in San Francisco, CA, often think their engineers are too smart to be phished. The reality? High-stress environments make people click. Training needs to be practical, short, and focused on the real-world threats they see in their inboxes every day.
- Gamified Learning: Use 5-minute interactive modules instead of hour-long snooze-fest videos.
- Report-a-Phish: Make it incredibly easy for employees to report a suspicious email with one click, and reward those who find "real" threats.
- Social Engineering Drills: Test your front-desk or CS team with phone-based pretexting to see if they’ll give up sensitive info to a "fake" CEO.
Why Do You Need an Incident Response Plan?
An Incident Response Plan (IRP) is the tactical playbook you follow when the "unthinkable" happens, reducing panic and cutting down recovery costs. In the middle of a ransomware attack, you don't have time to debate which law firm to call. A pre-defined IRP ensures that everyone—from the CTO to the PR lead—knows exactly what their role is in the first 60 minutes of a breach.
- The Communication Tree: Keep an offline list of emergency contacts, including your insurance broker, forensics partner, and legal counsel.
- Isolation Procedures: Know the specific technical steps to "quarantine" a compromised server without crashing your entire customer-facing platform.
- Post-Incident Forensic: Every "near miss" is a lesson. Use forensics to find the root cause and automate a fix so it never happens again.
How Do Monitoring and Continuous Improvement Work?
Continuous monitoring means using AI-driven tools to watch your logs for "impossible travel" or unusual data spikes that signal an active breach. Cybersecurity is a marathon, not a sprint. The best cybersecurity practices for startups require a feedback loop where you are constantly auditing your "Security Posture" and refining your defenses based on the latest threat intelligence from the San Francisco, CA area.
- Log Aggregation (SIEM): Centralize logs from your cloud, your code, and your endpoints so you can see the "big picture" of an attack.
- Annual Pen-Testing: Hire "friendly hackers" once a year to try and break into your systems. It’s better to pay them than to pay a ransom.
- Security Scorecards: Use tools to monitor your "public" security posture; this is often the first thing a VC looks at before a meeting.
How Do You Build a Security-First Culture?
Building a security-first culture means making safety a non-negotiable part of your "Definition of Done" for every project. When the founders talk openly about security and use the tools themselves, it signals to the entire company that data protection is a priority. It's about moving from "Security is the team that says no" to "Security is the team that lets us go fast safely."
- Security Champions: Embed one "Security-Minded" developer in every product squad to catch bugs early in the design phase.
- Transparent Post-Mortems: When a mistake happens, talk about it openly. Hiding breaches is how you get a "Culture of Negligence" that leads to massive fines.
- Simple Policy: If your security policy is 50 pages long, nobody will read it. Keep it to one page of "Golden Rules" that everyone can memorize.
What Are the Common Cybersecurity Mistakes to Avoid?
The most dangerous mistake a startup can make is assuming they are "too small to target" or relying solely on a single "shiny" tool. Hackers love small companies because they are often the "backdoor" into larger enterprise targets. Avoiding these "rookie" mistakes is what separates the survivors from the statistics in the 2026 digital landscape.
- Ignoring the "Human" Risk: Thinking tech can solve everything is a trap; social engineering is still the #1 breach vector.
- Delaying Compliance: Waiting until a "Big Fish" client asks for a SOC 2 to start your security program is a recipe for losing the deal.
- Poor Secrets Management: Storing API keys in .env files or hardcoding them into scripts is the fastest way to get your AWS account drained.
How Does Sentant Help With Startup Security?
Sentant acts as your outsourced CISO and "Boots on the Ground" IT team, building scalable security stacks that don't slow you down. We understand the unique pressures of the San Francisco, CA, startup world. We don't just give you a list of problems—we deploy the EDR, configure the MDM, and manage the 24/7 monitoring so you can focus on building your product.
- Virtual CISO (vCISO): Get the strategic guidance of a high-level security executive at a fraction of the cost of a full-time hire.
- Compliance Orchestration: We take the pain out of SOC 2 and HIPAA, handling the evidence collection and control implementation for you.
- Managed Security Ops: Our team watches your logs 24/7/365, reacting to threats in seconds to ensure your "Information Gain" stays protected.
Putting Your Cybersecurity Strategy into Motion
Protecting a startup in 2026 requires a shift from passive defense to active resilience. By integrating the best cybersecurity practices for startups—from hardware-backed MFA to immutable cloud backups—you aren't just checking a box; you are building a competitive advantage that enterprise clients value. Sentant is here to help you navigate this complex landscape, ensuring your digital foundation is as robust as your growth targets.
Don't wait for a "close call" to take your perimeter seriously. Implement the strategic framework today to protect your intellectual property and secure your company's future in the competitive San Francisco, CA tech ecosystem.
Schedule your free San Francisco cybersecurity audit today to learn more about how Sentant can harden your startup against the next generation of digital threats.
Frequently Asked Questions
Q: What is the "must-have" security tool for a 2026 startup?
A: A Managed Detection and Response (MDR) solution is essential. It combines 24/7 human oversight with AI-driven sensors to stop attacks like ransomware in their tracks before they can spread across your network.
Q: How does Sentant help with SOC 2 compliance in San Francisco?
A: We provide the "technical muscle" for compliance. We implement the necessary controls (like MFA, encryption, and logging), gather the evidence for auditors, and act as your security lead during the entire examination process.
Q: Why are AI-powered attacks more dangerous for startups?
A: AI-powered attacks can "research" your company and mimic your employees' writing styles in seconds, making phishing nearly impossible to detect. They also adapt their malware in real-time to bypass traditional signature-based antivirus.
Q: Is Cyber Insurance worth the cost for a small startup?
A: Absolutely. In San Francisco, CA, the cost of a forensic cleanup and legal notification can easily exceed $500,000. Cyber insurance provides the financial safety net needed to recover from a major breach without going bankrupt.
Q: How do we secure a fully remote team without a central office?
A: Focus on "The Three Pillars": Secure the Identity (MFA), Secure the Device (MDM), and Secure the Connection (ZTNA). When you control the user and the laptop, the physical location of the employee no longer matters for security.
Will Pizzano, CISM is Founder of Sentant, a managed security and IT services provider that has helped dozens of companies achieve SOC 2 compliance. If you’re interested in help obtaining SOC 2 compliance, contact us.